From our best comments
Avira Software Updater for Windows
Easily fix security flaws in your software, such as video-conferencing apps like Zoom
- Updates your software and drivers
- Optimizes your hardware’s performance
- Rids you of update reminders (Adobe, Google, Skype, etc.)
Millions of reasons to trust Avira
Installed Software Updater, relying on Avira to keep their software safe and up-to-date.
That’s how many our software runs every year – saving you time and effort
That's 30 years of protecting our users' devices and privacy.
Why not just use Windows Update?
A lot of people think that their Windows Update app is all they need. But they’re wrong. Windows Update only updates Windows software. And that leaves a bunch of third-party software and drivers vulnerable to security flaws. Software Updater is designed to remove this worry.
Compare Free vs. ProSimple, elegant, and easy to use: Get even more with Pro

Avira has more than 35 years of online security experience
System Requirements
Free software updater for Windows
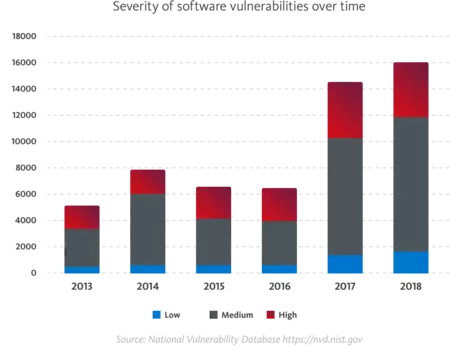
A software updater gives you the latest software features and enhanced performance, plus protection from dangerous security flaws in outdated software — something which are an even greater security risk than malware, and a popular gateway for cybercriminals who often exploit these vulnerabilities to gain access to sensitive data and/or plant malware. You can easily protect yourself against these exploits by using a program updater to help you keep your software and drivers up to date and fix security flaws.
Programming errors are the most common cause of software vulnerabilities. Once they’re discovered, they’re usually fixed quickly by a security update — or what is also referred to as a security patch — which involves simply replacing the defective software component with a corrected version without the need to update the entire software product. If the defect is deemed critical enough and poses a significant security risk, a hotfix or quick-fix is applied as quickly as possible. If an error is found in a program’s source code, this is referred to as a bugfix.
The various types of software update differ mainly in terms of their scope:
- Patch: A small correction for programs, drivers, and operating systems that fixes the particular bug or security flaw.
- Software update (service release): A collection of multiple individual patches and possibly minor enhancements and additional features.
- Update package (cumulative update): A bundle of multiple software updates in one package.
- Software upgrade: A new version of the software product based on the preceding version, offering major improvements and additional features.
Protect yourself with secure updates for your software and drivers
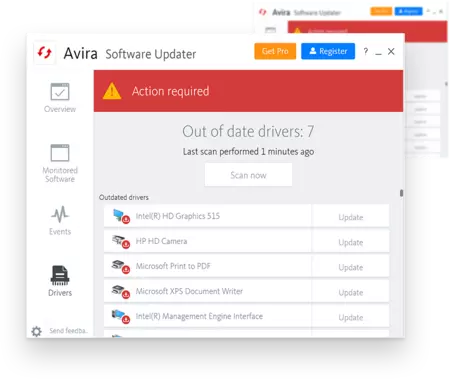
Unlike your Windows Update app which only keeps Windows up to date, Avira Software Updater Free keeps both Windows and popular third-party software up to date. After you’ve opened Software Updater and run a scan, you’ll see a list of programs for which an update is available. You can then easily download and install any software updates directly from the publisher’s website using the update link next to the program name. Thanks to Software Updater, this means you don’t have to waste time searching for the latest updates yourself — plus you can prevent malicious updates from getting on your PC, which may be hidden in fake pop-ups that look like legitimate Windows update notifications.
With Avira’s free system updater, you can also keep your drivers up to date for enhanced system stability. Outdated drivers can cause a range of issues, including crashes and errors. With updated device drivers, your operating system can communicate smoothly with built-in components such as the graphics card and connected hardware such as printers or scanners. Outdated drivers can also cause communication issues, leading to malfunctions and performance problems. A driver updater such as Avira Software Updater also scans your hardware, monitors the version of active drivers, and notifies you of fresh updates. Updating your software and drivers regularly is a really easy way to ensure your system is always stable.
Enjoy even more advantages with our premium system updater
Avira Software Updater Pro saves you time and effort as you can get it to update your software and drivers automatically. This is all thanks to the software update manager included in the premium program, which allows you to create an update list. As soon as an update is available for one of the programs on your list, it is downloaded and installed automatically in the background without you having to lift a finger. If you want, you can even update individual programs in just a few clicks.
Avira Software Updater Pro is also included in our all-in-one Avira Internet Security solution. Besides our premium software updater, this practical bundle includes our premium antivirus protection solution Avira Antivirus Pro and Password Manager Pro with extra protection for your online accounts. If you want even greater convenience and features, Avira Prime — our most feature-packed solution — is the one for you. In addition to the above, it includes Avira Phantom VPN Pro with unlimited traffic for secure and anonymous surfing as well as System Speedup Pro with many tune-up tools to boost performance and free up disk space.
Avira Software Updater — the indispensable tool for Windows users
Enjoy a host of additional benefits alongside protection against security flaws and errors with our free software updater for Windows. Say goodbye to annoying update notifications disturbing you while you work, and instead schedule software updates at a time that suits you — really handy for when you need to restart your computer following an update. A software update manager also helps you manage and monitor your program and driver updates all from one dashboard.
Besides many other tools, including antivirus protection, VPN, password manager, PC cleaner, and browser safety add-on, the free version of Avira Software Updater is also included in our everything-in Avira Free Security suite. It’s all you need to keep your software and drivers up to date, plus protect your computer against online threats, generate and store secure passwords for all your user accounts, surf anonymously, and clean up and speed up your devices.
By updating your software regularly, you get to enjoy all the latest features, improvements, and corrections as well as greater protection as updates plug dangerous security holes. These are usually caused by programming errors and, once discovered, a software update quickly fixes them so that cybercriminals cannot exploit them. Avira Software Updater for Windows notifies you about outdated programs, providing you with the latest software updates for download.
Depending on your internet connection speed, computer hardware, and the type and scope of the update, the time it takes to download and install a Windows update can vary quite a bit. As an example, updating from Windows 10 to Windows 11 usually takes between 20 and 60 minutes. However, if you want to update from a very old version of Windows to a more recent one, you should allow significantly more time since many cumulative updates might need to be downloaded.