Solutions

Anti-malware
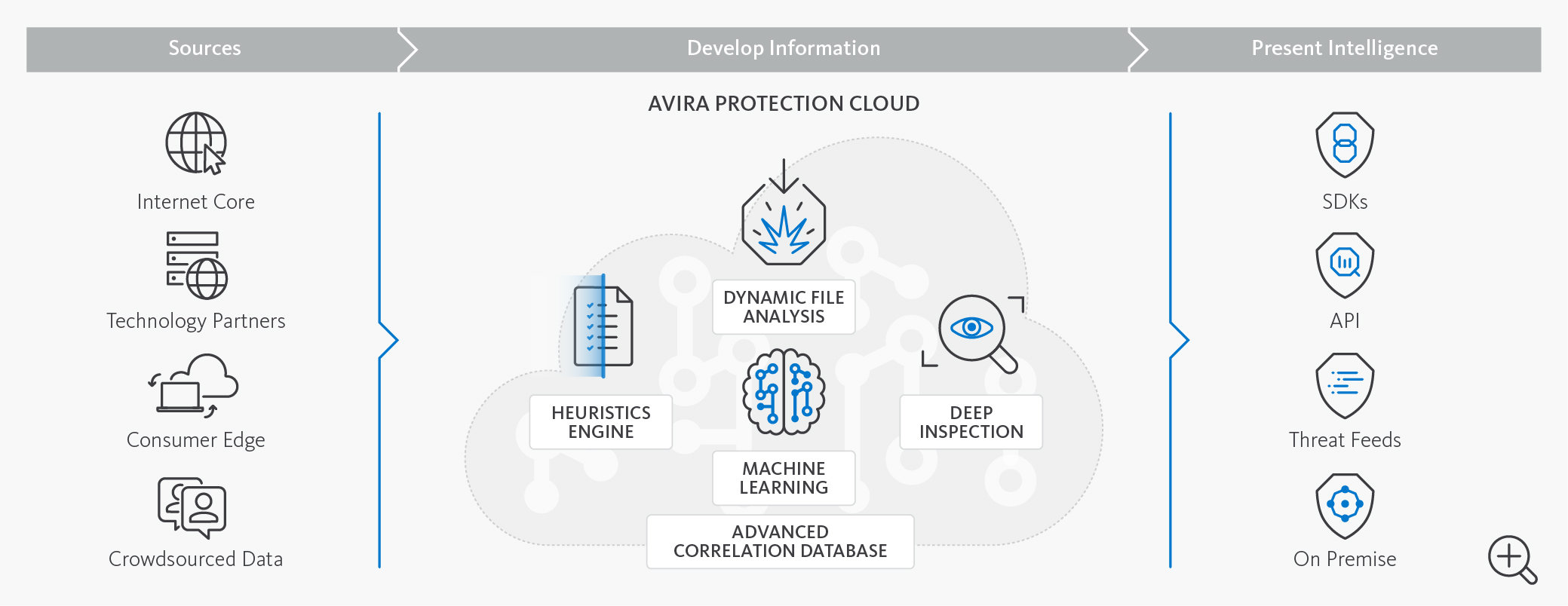
Build your own security solutions with our anti-malware SDKs and software utilities: Based on our award-winning technologies.

Threat Analysis
Access Avira's world-class threat intelligence directly, submit files and URLs for analysis. On-demand, priced by volume and usage.

Threat Intelligence
Avira’s threat intelligence is unique because it delivers comprehensive, clear and simple to consume intelligence as a machine readable feed.