Researchers have found that over a thousand Android apps are tracking users – even when the apps were not given permission to do so. In their quest for data, the suspect apps were collecting data from other apps, metadata tags from photographs, and call logs — all without getting explicit permission from the device owner.
The study from the International Computer Science Institute found that over 1,300 Android apps were gathering data from devices even after people explicitly denied them permission. The researchers’ findings were presented by Serge Egelman, ICSI director of usable security and privacy research at the Federal Trade Commission’s PrivacyCon event this June.
“Fundamentally, consumers have very few tools and cues that they can use to reasonably control their privacy and make decisions about it,” Egelman said at the conference. “If app developers can just circumvent the system, then asking consumers for permission is relatively meaningless.”
What happened to just asking for permission?
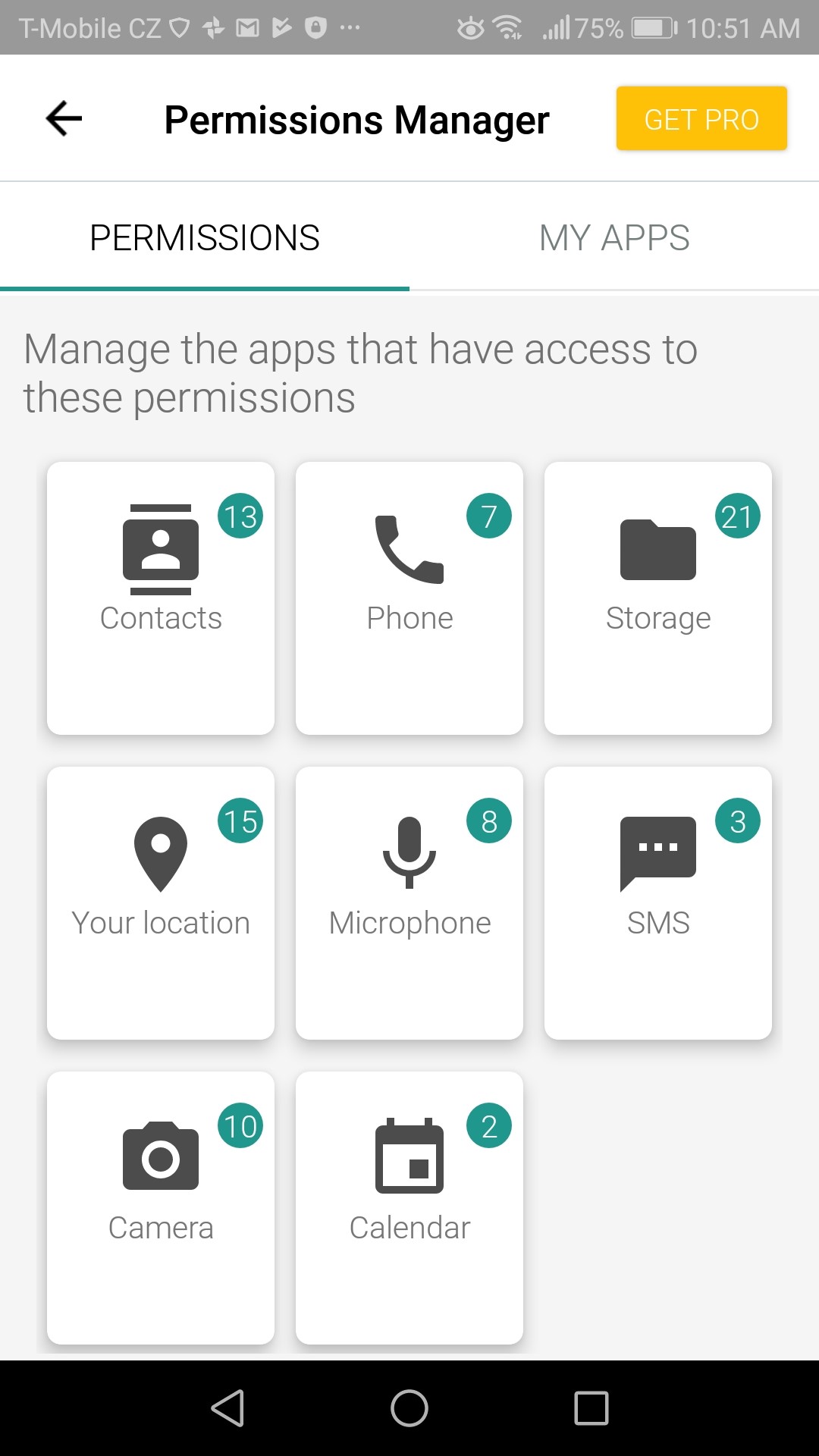
Android phones let users decide in the Settings/Apps & notifications folder what types of data the individual apps installed on the device can access. Users can toggle access on-or-off for each app.
The same information is also available in many security apps such as Avira Antivirus for Android. These are the very tools that Egelman was talking about.
Despite the dire warnings that some apps give when access is turned off – people could believe that they were able to control app access to their device and private data – at least until this report came out. Now it is clear – your stated permission choices just do not matter for many apps.
How did they circumvent my privacy choices?
The 1,300 apps violated user privacy choices by using workarounds in their app coding that let them take data from various sources like WiFi connections and the metadata that’s part of most digital photos. Shutterfly for example, a photo-editing app, was caught gathering GPS coordinates from photos and sending that data to company servers, even when users had declined against giving the app location data – a charge subsequently denied by Shutterfly.
Invasive apps can piggyback on other apps
Some of the identified apps were eavesdropping on the data harvesting by other apps. Thanks to coding tweaks, these apps could read unprotected files on a SD card or collect phone details like an IMEI number via other apps with this ability and level of permission. One of the most notable apps with this capability was Baidu’s Hong Kong Disneyland park app. Samsung’s Health and Browser apps also had this cross-referencing ability.
You can (hopefully) protect yourself
The basic security step is to check – either directly in Android or via your antivirus app – what permissions you have already granted the various apps on your phone. While looking, check to make sure that the permissions granted are in line with what the app requires.
If the permission seems odd – just turn it off. But, as this research showed – what one app has been granted permission to do just might be intercepted by another app.
We will find out the 50 ways apps leak our data
The full list of apps circumventing user permissions will be released this August by Egelman and the team of researchers at the Usenixsecurity conference in a paper titled “50 ways apps leak our data.”
An Android update should fix this permissions problem
This privacy issue is expected to be addressed and maybe solved in Google’s Android Q update, scheduled for release later this year. Given the fragmented Android system for delivering updates, it might take a while for this update to reach the end users.