You probably know that a firewall is a powerful tool in your computer’s security arsenal. But what exactly is behind it? Read on to learn all you need to know about firewalls, like which categories and types of firewall there are, how they work, and what they’re needed for. Also discover how to improve your firewall’s protection and strengthen it with the additional protection features of Avira Free Security.
What does a firewall do?
Most nightclubs have a bouncer who keeps an eye on the door so only the “right” or invited guests get in, denying entry to potential troublemakers. A firewall works in a similar way, but does its job much more discreetly and unnoticed in the background.
A firewall is a basic security device that controls data traffic between two networks, usually a public (external) network such as the internet and a private (internal) network. It protects a single computer or an entire network from unauthorized access and cyberattacks, preventing intruders from snooping on your personal data or injecting malware like Trojans and other spyware onto your device. In a nutshell, a firewall ensures you can surf more safely.
Compared to a bouncer, a firewall monitors not only incoming but also outgoing data traffic for potentially harmful and suspicious activities. It verifies traffic based on rules that either allow or deny data transfer. A firewall can only be as good as its predefined rules — if malicious traffic is not defined as such, it can neither be detected nor blocked. This makes it a good idea to have a good in-house IT security service or powerful antivirus protection on your PC that immediately detects and neutralizes unwanted intruders.
A firewall is included as part of the operating system on every Windows and Mac computer, and is always running by default. Your internet router also usually has a firewall to protect your home network. The firewall in a DSL router monitors the data traffic that enters your network from outside or goes from your network to the internet. By contrast, the firewall integrated into your computer’s operating system controls the data traffic on your PC. This means there are two different firewall categories, which we’ll now take a closer look at.
Hardware versus software firewall
Depending on where the firewall software is installed, a distinction is made between a hardware firewall — also called a network firewall, network-based firewall, or external firewall — and a software firewall, which can also be referred to as a personal firewall, desktop firewall, or host-based firewall. Even though the terms hardware firewall and software firewall suggest otherwise, a firewall system always contains a software component.
In principle, both firewall categories work in a similar way, but they differ conceptually. Compared to a software firewall, a hardware firewall doesn’t work on the system to be protected itself, but on a separate device that protects all computers connected to the network and is physically connected upstream of them. Firewalls that run on dedicated devices typically offer comprehensive security features and are more complex, more powerful, and less susceptible to tampering. The specially developed hardware boasts powerful processors, memory, and network interfaces that are optimized for use as a firewall.
These firewalls are a combined system comprising hardware, an operating system, and bespoke firewall software. The hardware may contain components such as network interfaces to connect networks, network segments, or subnets. The corresponding firewall software regulates access between them, ensuring that threats cannot spread.
While the software of a hardware firewall can monitor data traffic between different network types thanks to this network segmentation, the software of a software firewall inspects the computer’s connections to and from communication partners within a local network as well as to external networks.
Since hardware and software firewalls complement each other and can strengthen protection, they’re used jointly primarily in companies and public institutions or any areas where sensitive data is kept. The range of features and the technology used can vary greatly depending on the type of firewall — we’ll dive into the different firewall types and filtering techniques in more detail later on.
Your PC’s pre-installed firewall is a software firewall and your internet router is a hardware firewall. Even though your router’s firewall only has basic security features compared to dedicated devices, it usually offers sufficient protection for private use.
Here are some tips to help you optimize your firewall protection and get the most out of it.
How to use your firewall correctly
- Keep your firewall up to date. Regularly update your operating system and firewall software so your firewall protection is always up to date.
- Never turn off your firewall. Turning off your firewall is generally not a good move, especially not permanently. If you find one of your trusted applications is blocked, you can add an exception for that program and allow access to the internet. This means you don’t have to turn off your firewall and expose your device to unnecessary risks.
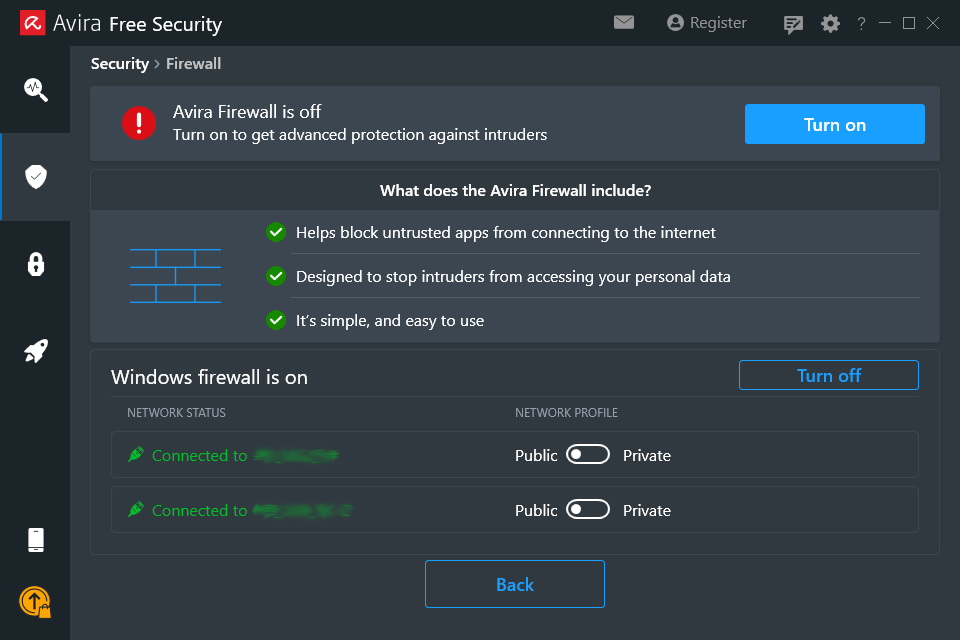
- Optimize your firewall settings. Windows users can do so easily using settings tools such as Avira Firewall Manager, which is included with Avira Free Security, to configure the pre-installed firewall in granular detail. In the Security > Firewall area, you can set up rules for individual programs and ports as well as for IP addresses and IP address ranges and combine several filter criteria — you can of course also simply accept the recommended settings.
- Strengthen your router security. Since your DSL router is your gateway to the internet and the heart of your home network, you should also keep its firewall on and up to date. Thankfully, though, firmware updates are often installed automatically.
- When using a public Wi-Fi hotspot, adjust your firewall settings and/or use a VPN. Since public Wi-Fi hotspots are often unsafe or insufficiently secured, Windows users can use the firewall’s public network profile instead of the private network profile to apply more restrictive settings. Mac users can enter stealth mode to ensure their Mac is not easily discovered by other users on the same network.
However, a firewall cannot protect your device from threats posed by other devices on an unsecured Wi-Fi network or from fake hotspots — just as little as it can against man-in-the-middle attacks, which can intercept traffic between your laptop and the internet. In this case, a virtual private network (VPN) will help encrypt your online traffic to protect it from unauthorized access. - Install and enable additional security solutions. Equip your firewall protection with additional defenses to protect yourself against cyberthreats that the firewall doesn’t safeguard against. In addition to the already mentioned Avira Firewall Manager, the all-in-one solution Avira Free Security includes powerful antivirus protection, a VPN, and much more.
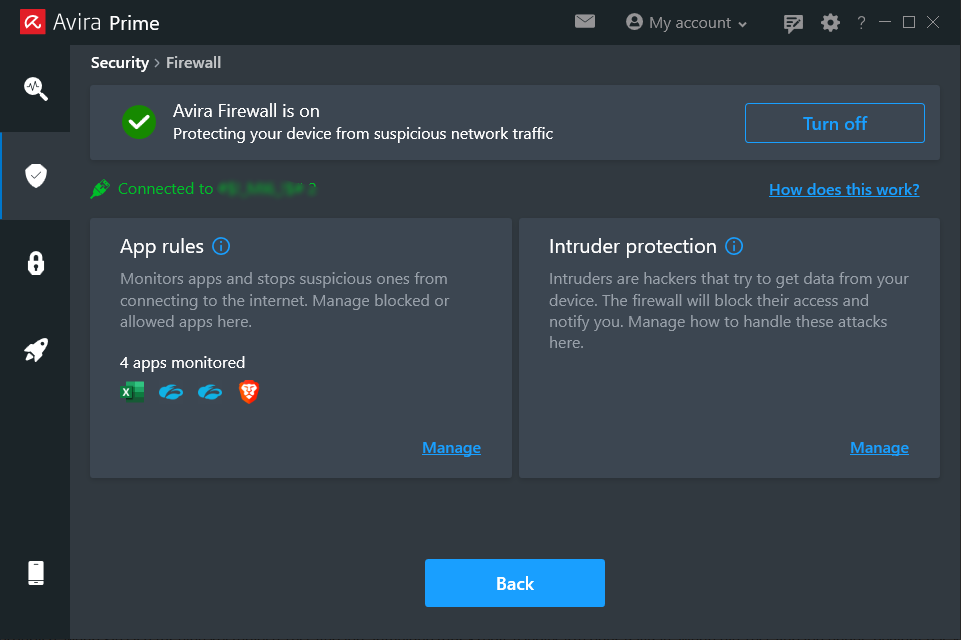
Top tip: Use the Avira Firewall as an additional layer of protection
Among many other additional features, the advanced cyberprotection solution Avira Prime also offers you your own firewall in the form of the Avira Firewall. It complements your pre-installed Windows firewall and helps make your PC even more secure.¹ It’s designed to monitor applications and block potentially risky programs before they can cause damage — including suspicious and unauthorized applications trying to share your personal information. The Avira Firewall helps you protect your computer even better against intruders and attacks on your system, notifying you when one has been repelled.
How does a firewall work?
Before we look at the different filtering techniques and firewall types, let’s first take a general look at how computers communicate with the internet.
Communication on your PC takes place via “doors” called ports, which can be opened temporarily. Since each port is reserved for a specific process or service, and is assigned a corresponding number, data packets can be assigned to a specific application. This means your computer “knows” whether you want to send an email, download a document, or visit a website. It then opens the appropriate door to allow the traffic in and out.
If such a port is open, theoretically anyone can use it to send or receive data over the internet. The more ports that are open, the more potential entry points there are and the easier it is for intruders to gain access to your system. This is exactly where a firewall comes in, blocking ports based on certain rules and closing ports that are not needed to protect against unauthorized access.
By the way, there are specific TCP ports that are really attractive targets for cyberattacks because they use frequently used protocols and services. These include port 80 for HTTP (Hypertext Transfer Protocol) or port 443 for HTTPS (Hypertext Transfer Protocol Secure).
This makes it all the more important to carefully configure your firewall based on the network’s security policies and requirements. Among other things, the configuration determines which ports should be open for data traffic for normal network operation and which ports should be closed or blocked for network security.
However, this is only one of several methods to control data traffic. Another is to block traffic coming from a specific source IP address or which is directed to a specific destination IP address. In addition, traffic can also be blocked based on a protocol that’s used, a specific application, or based on behavior or content.
For this purpose, filter techniques are used that work at different levels of the Open Systems Interconnection (OSI) model. This reference model includes seven layers, which each use specific functions and protocols to enable efficient communication between devices. A distinction is made between the four network-related and the three application-related layers, which we refer to here as the network and application layers.
What filtering techniques and firewall types are there?
Today, there are a variety of firewall types and filtering techniques used to protect networks and computer systems from unwanted traffic and potential threats. Firewalls can vary greatly in their range of functions and combine different technologies, which is why these mixed forms are also called hybrid firewalls.
From simple rules-based packet filter firewalls to advanced next generation firewalls with intrusion detection and prevention systems (IDPSs) right through to centralized unified threat management solutions, there are a wide range of firewall types and systems, some of which can no longer be clearly distinguished from one another. In some cases or contexts, the designation of a firewall type refers to the technology that’s used (packet filter firewall), in others to the operating level (network firewall), and in others in turn to the placement (cloud firewall) or the location of use (hardware firewall) or the generation (next generation firewall), making clear categorization also difficult.
The main types of firewall include:
Packet-filter firewalls/stateless firewalls (network firewalls) — 1st generation
As the name suggests, static or stateless packet filtering (SPF) is used. This is the oldest and comparatively most rudimentary type of filter technology, which has been enhanced over time. Packet filter firewalls operate at the network level and perform stateless packet inspection. This means that various parameters of a data packet are checked independently of previous packets, in other words statically. Here, the header information of the individual data packets, meaning smaller amounts of data that together make up the incoming data traffic, is evaluated individually. This includes the port numbers and IP addresses of the senders and recipients as well as the protocol type.
Stateful inspection firewalls (network firewalls) — 2nd generation
Here too, the name says it all: Stateful inspection firewalls, or stateful firewalls, use dynamic packet filtering or stateful packet inspection (SPI). Compared to simple packet filtering, inspection is done statefully. This means that in addition to static packet filtering, the status of a network connection is included in the inspection. This involves data packets being assigned to a specific active session and analyzed in the context of this connection. For example, when you visit a web page, a stateful firewall detects the active TCP connection between your computer and the web server, and can allow or block data packets based on the session status.
Application firewalls and web application firewalls
An application layer (or level) firewall (ALF), or application firewall for short, is a collective term for firewalls which, compared to “pure” network firewalls, monitor and control data traffic not only at the network level but also down to the application level. Through more detailed analysis, they can protect various applications and services and their data from cyberthreats.
A web application firewall (WAF) is a special type of application firewall. It monitors HTTP and HTTPS traffic between web browsers and web servers to protect web applications from application-specific attacks. A web application firewall protects both the web application on the web server as well as the web server itself.
Application firewalls also include proxy and next generation firewalls (NGFWs), which we’ll take a brief look at in the following sections.
Application firewalls can include the following filtering techniques:
URL filters: This technique allows a firewall to control access to websites based on their URL addresses. The firewall compares the requested URLs with a list of allowed or blocked websites and then decides whether access itself should be allowed or blocked. URL filters are often used to restrict access to inappropriate or dangerous websites and to increase network security.
Web filters: Unlike URL filters, which work on the basis of URLs, a web filter analyzes website and web-application content to block or control access to unwanted content. This may include blocking certain file types, scanning web applications for security vulnerabilities, or detecting malicious code. Web filters can also be content filters, which is why both terms are sometimes used synonymously.
Content filters: These can be implemented as part of web filtering or as a standalone feature. They monitor and analyze the content of data packets or web pages to identify and block unwanted or malicious content. This may include certain file types (such as executable files or archive files), malicious code (like malware or exploits), or inappropriate content (such as violent or pornographic content).
Proxy firewalls
Proxy firewalls are a special type of application firewall that can use multiple proxy filters specialized for certain application protocols. A proxy-based firewall acts as an intermediary (proxy) between the client and the server. It receives the client’s requests on behalf of the client, inspects them, and then establishes a separate connection to the target server. Since the device and network never communicate directly with each other, with the firewall mediating between the internal and external system, it’s considered a very secure firewall.
Next generation firewalls (NGFWs) — 3rd generation
This state-of-the-art application layer firewall can combine multiple technologies, offering functionality that goes far beyond that of traditional firewalls. This means NGFWs can also fend off very complex cyberthreats and offer significantly higher levels of protection. Additional components can include security features such as a VPN, intrusion detection/prevention systems (IDSs/IPSs), and other unified threat management (UTM) services.
Among other things, next generation firewalls use deep packet inspection (DPI) — an advanced form of stateful packet inspection. It inspects not only the header but the entire content of a data packet for certain keywords as well as patterns or signatures that may indicate malicious content. Threat-focused next generation firewalls go one step further still, using advanced technologies such as machine learning, artificial intelligence, behavioral analytics, and heuristic approaches for signature-free detection. This also enables them to identify emerging threats and proactively protect against previously unknown attacks.
Cloud firewalls and virtual firewalls
Cloud firewalls are specifically designed for use in cloud environments. They monitor traffic between the internet and cloud resources, such as cloud platforms, data stored in the cloud, infrastructure, and applications. Cloud-based firewalls can also protect the internal/private network across multiple locations within a company using a VPN. They can be provided as a firewall-as-a-service solution by a third party or implemented as part of a cloud security solution.
Virtual firewalls run as a virtual appliance or software solution on a virtual machine or cloud server and can be used in various environments, including local data centers, private clouds, or public clouds. Cloud providers can offer them as part of their cloud services or organizations can deploy and manage them themselves.
In principle, any type of firewall can be deployed in the cloud or implemented as a virtual firewall, since the designations only refer to the implementation environment and the context in which the firewall is used — just like the hardware and software firewalls discussed at the beginning.
Do mobile devices have firewalls?
Android and iOS smartphones do not have integrated firewalls in the traditional sense, but they do contain security features that perform similar tasks. Since the architecture of smartphones is very different from computers, they’re based on a different security model that’s considered comparatively secure. Among other things, the model relies on an isolated execution environment for apps, restricting access to system resources and other apps’ data. That’s why your device asks you for permission — such as for access to the camera or your contacts.
As long as you use your home Wi-Fi or mobile network, the risk of outside intrusion is relatively low. When surfing using your mobile data, the data is transmitted encrypted between your device and the mobile operator’s base station. However, the situation is different when using unsecured public Wi-Fi hotspots. In this case though, as already explained, even a firewall wouldn’t offer any protection — but a VPN would. It helps you both encrypt everything you send and receive online even on your smartphone and protect your data from snoops.
A VPN is included in many security apps like Avira Antivirus Security for Android and Avira Mobile Security for iOS. The Android app also helps protect a smartphone from mobile threats such as malware, which can hide in apps and get onto your device. It also includes a permissions manager that allows you to check which access rights your apps have.
Go for an all-in-one solution
A firewall is essentially the first line of defense for your PC and an essential part of its security system, but it won’t protect it from every online threat — especially since only SPI firewalls are usually used for private use, and they lack URL, web filtering, and other features. In addition, a firewall cannot prevent attackers from exploiting vulnerabilities in outdated software to gain access to your system.
To protect your data and devices comprehensively, we recommend using a free all-in-one solution like Avira Free Security which includes many other features in addition to antivirus protection and a VPN. These include a software updater for Windows to close security holes in programs as well as a browser safety extension to block malicious websites and content.
So, beef up your computer’s bouncer with additional security personnel for greater cybersecurity provided by a powerful team.
¹ The Avira Firewall works independently, even if Windows’ pre-installed firewall isn’t running.














