Ransomware attacks keep taking the world by surprise, as the latest widespread ransomware WannaCrypt0r (also known as WannaCrypt, WannaCry, or WCry) shows in a rather sad scenario, that affected tens of thousands of users, companies, and even hospitals, in over 90 countries. Despite us, as security experts, advocating for extra caution on the topic it is easier to pretend things like that will happen only to others and go on as before.
Unpleasant as they are massive ransomware attacks have been expected to increase in both frequency and intensity for some time now. We are actually witnessing an entire cyber crime branch being built on this type of attacks, as they allow for millions of dollars to be raised from the victims with relative ease.
What is ransomware?
There are two types of ransomware: crypto-ransomware that encrypts files (rendering them unreadable), and screen-locking ransomware that locks the home screen. In both cases, the authors of malicious software demand a ransom from its victims to access the files and device.
Ransomware is frequently spread via email: a cyber criminal sends an email with an attachment. The unsuspecting user opens the document (or javascript file), which looks like gibberish. The document recommends enabling macros “if the data encoding is incorrect,” which, of course, it is by design. Enabling macros allows the ransomware to be secretly downloaded onto computers via a drive-by download.
What is so special about WannaCrypt0r?
In this case, it’s the ransomware’s way of spreading, which is more like a worm than a “normal” ransomware. That means that once it is on your PC it will try and spread to another one on its own and by means of exploiting vulnerabilities that have either not been detected or patched yet. In the case of WannaCrypt0r, it’s a vulnerability called EternalBlue – one of the exploits recently released by Shadow Brokers in the leaked NSA tools archive. Ironically there is already a patch available by Microsoft for all affected Windows systems since March which shows how seldom updates are actually conducted by individual users and bigger companies alike. Following the attack Microsoft has even released patches for Windows XP, Windows Server 2008 and most other operating systems they no longer support but that are still widely used.
“I cannot stress how utterly important it is to have your system up to date,” says Oscar Anduiza, malware analyst at Avira. “In a perfect world where everyone had installed this patch, an attack like this would have been unthinkable”. So if you haven’t done so people, get to it and update your OS. By the way, with our Software Updater Pro you would have had the patch installed on your system the day it was released without any hassle and with just one click – so there is really no excuse to leave this vulnerability wide open for any ransomware to exploit.
How does WannaCrypt0r work?
After finding a way on the PC via the above exploit it will try and get full permission to execute and encrypt the system. The command it’s using is “icacls . /grant Everyone:F /T /C /“. It even goes so far and kills the mail storage and whatever other databases the user has on his or her PC in order to get to those as well.
Once done, it searches for files with the extensions “.der, .pfx, .key, .crt, .csr, .pem, .odt, .ott, .sxw, .stw, .uot, .max, .ods, .ots, .sxc, .stc, .dif, .slk, .odp, .otp, .sxd, .std, .uop, .odg, .otg, .sxm, .mml, .lay, .lay6, .asc, .sqlite3, .sqlitedb, .sql, .accdb, .mdb, .dbf, .odb, .frm, .myd, .myi, .ibd, .mdf, .ldf, .sln, .suo, .cpp, .pas, .asm, .cmd, .bat, .vbs, .dip, .dch, .sch, .brd, .jsp, .php, .asp, .java, .jar, .class, .wav, .swf, .fla, .wmv, .mpg, .vob, .mpeg, .asf, .avi, .mov, .mkv, .flv, .wma, .mid, .djvu, .svg, .psd, .nef, .tiff, .tif, .cgm, .raw, .gif, .png, .bmp, .jpg, .jpeg, .vcd, .iso, .backup, .zip, .rar, .tgz, .tar, .bak, .tbk, .PAQ, .ARC, .aes, .gpg, .vmx, .vmdk, .vdi, .sldm, .sldx, .sti, .sxi, .hwp, .snt, .onetoc2, .dwg, .pdf, .wks, .rtf, .csv, .txt, .vsdx, .vsd, .edb, .eml, .msg, .ost, .pst, .potm, .potx, .ppam, .ppsx, .ppsm, .pps, .pot, .pptm, .pptx, .ppt, .xltm, .xltx, .xlc, .xlm, .xlt, .xlw, .xlsb, .xlsm, .xlsx, .xls, .dotx, .dotm, .dot, .docm, .docb, .docx, .doc“, etc. and stores a @Please_Read_Me@.txt ransom note and a copy of the @WanaDecryptor@.exe decryptor in every folder where a file was encrypted.
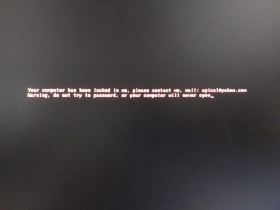
To aggravate the removal, WannaCrypt0r also makes sure to eliminate the shadow volume copies, disable the Windows startup recovery, and clear the Windows Server Backup history. Here is where the user comes in because in order to being able to run the command line parameter needed for those actions the ransomware has to have the user’s permission. That leads to an UAC prompt that pops up and which the user has to accept. If he does not he may still have the chance to restore his system. If he does, this is the point of no return: WannaCrypt0r will run the command line “cmd.exe /c vssadmin delete shadow /all /quiet & wmic shadowcopy delete & bcdedit /set {default} boostatuspolicy ignoreallfailures & bcdedit /set {default} recoveryenabled no & wbadmin delete catalog -quiet” and, after the removal of the shadow copies, show a typical ransomware block screen and desktop.


Avira offers security of mind and for your PC
While we are still continuing to investigate the details of the WannaCrypt0r attack – after all a malware analyst’s job is never done – we can already confirm that our software successfully detects it, as variants of the ransomware have first been detected by our scans approximately two months ago.
But be it ransomware, phishing or privacy, nowadays there is almost no excuse to fall victim to a cybercrime anymore. Our extensive 360° security portfolio offers a solution for everything and can prevent most things before they even have a chance to happen:
Be one step ahead, prevent an attack
Our Software Updater Pro, the Scout Browser, Phantom VPN Pro and the Avira Password Manager offer the perfect package to prevent anything from happening in the first place. Where the Software Updater makes sure that vulnerabilities are closed as soon as a patch is available, the Scout Browser, VPN, and Password Manager defend your data from falling into the wrong hands. Falling prey to any kind of malware and phishing campaign will be a lot harder this way.
Detect it before it has a chance to grow roots
Our distinguished Avira Antivirus Pro with its enhanced ransomware protection will protect you no matter what. Be it a normal virus, worms, malware, or ransomware – it’s got you covered and offers a piece of mind you’d otherwise not have.
Clean up behind you
In case you notice too late that you probably would have needed an Antivirus and your PC seems lost our Avira Antivirus Pro has a rescue system that might just save you. And if that’s not enough System Speedup makes sure to optimize your PC afterward and fixes errors, repairs broken settings, and cleans your system registry.