Whether it’s a grandchild in need, a Nigerian prince with too much money, or a bank spreading fear and terror — we’ve probably all come across social engineering scams at some point, even if we may not all be familiar with the term. In today’s digital age, there are countless ways and means to manipulate, deceive, and cheat people. Read on to learn what exactly is meant by social engineering, what tricks cyberscammers use, and how you can protect yourself from social engineering attacks — such as with a cybersecurity solution like Avira Free Security.
What is social engineering?
Scamming is one of the oldest tricks in the book. Who hasn’t heard reports of some elderly person being defrauded of vast sums of money by some scammer who called them up and told them some crazy story?! In many cases, tricksters are even very successful with the grandparent scam, where they pretend to be a close relative in need.
Increasing digitalization is opening up opportunities for scammers that their like could only dream of not so long ago. That’s because it’s never been easier to pretend to be someone else and reach so many potential victims — all thanks to digital communication channels and social media platforms. Among others, you’ll also see the grandparent scam popping up on messaging services like WhatsApp.
The term social engineering has taken root to describe scams in the digital age. It originates from the realms of social and political sciences where psychological manipulation is used on groups to improve their social behavior. Today, however, the term social engineering is used primarily to refer to a type of cyberthreat, and in this context describes exclusively negative rather than positive manipulation methods.
Social engineering as an attack strategy
Social engineering involves attack strategies that target human rather than technical vulnerabilities. That’s why social engineering is also called human hacking or social hacking. The term encompasses a wide variety of different methods and tactics that cybercriminals can use to induce certain behaviors through manipulation, deception, and misrepresentation — almost always hurting or harming their victims.
In the case of social engineering attacks, cyberscammers try to trick users into revealing confidential information or sensitive data, download malware like ransomware or spyware, or transfer money. To do this, they deceive their potential victims about their identity and intentions, and make false promises, say something terrible is going to happen, or ask for help. Worst still, their creativity knows no bounds when it comes to achieving their aims.
How and why does social engineering work?
Cyberscammers, also known as social engineers, exploit fundamental human emotions, characteristics, and behaviors for their own purposes. They scare us, arouse our curiosity or appeal to our compassion, promise love or money, or lure us into their trap with lucrative offers and alleged winnings.
To do this, they use all communication channels available to them: They can carry out their social engineering attacks via email, telephone, texts and messaging services, social media platforms, or online dating portals. In social networks and dating apps, they can create deceptively real-looking profiles, also known as catfishing, or even assume the identity of actual people.
For their social engineering attacks, the scammers can take on any role and pretend to be a trustworthy or close person (friend, relative, colleague, employer, etc.) or a reputable institution (bank, government agency, company, etc.). Sometimes they also pretend to be a customer support employee or system engineer for a service or online shop we use.
In doing so, they rely on our respect for authority, our loyalty to the state, our fundamental trust, our general willingness to help, or likewise our human greed. Let’s take a closer look at some of the tactics:
- Arouse curiosity: Cybercriminals might send links to seemingly interesting offers or media content.
- Request or offer help: The scammers ask for financial support in an alleged emergency. Or they offer their own help, such as to fix a supposed technical issue or to improve the security of an online account.
- Scare: In some cases, they scare you into believing you’re going to lose money due to an allegedly compromised account, that your account’s going to be blocked, or that the police or debt collectors are coming to get you. Time pressure often comes into play as another lever here.
- Make promises: Another very effective social engineering strategy is to offer free deals, prizes, cash gifts, or even affordable housing and attractive job offers.
Untargeted and targeted social engineering attacks
Untargeted social engineering attacks use a broad range of tactics to target a large number of randomly selected people or groups of people. Among other things, phishing emails that either target sensitive data or attempt to inject malware fall into this category.
In targeted social engineering attacks, cyberscammers gradually gain the trust of their victims. In contrast to sending phishing emails en mass, this approach is much more tedious and time-consuming, but can also be more lucrative if successful.
An example of this type of social engineering attack is spear phishing, where cybercriminals often try to gain access to confidential company information. The more a scammer knows about the target company and its employees, the better the deception works and the more targeted their actions can be. To achieve their aims, they collect information via social networks, calls, and emails and then contact a specific target person who has access to sensitive areas of a company. Armed with this background knowledge, they can often pose very convincingly as a service provider, business partner, customer, or colleague and gain access to highly sensitive information. Pretexting is often used here, which we’ll look at in more detail below.
Popular social engineering methods and strategies
In the following, we present some of the methods and strategies used by social engineering scammers that you’ve probably heard of — or may even have been a victim of yourself. After all, it’s not only highly gullible people who fall for sophisticated social engineering tricks.
In addition to the technical forms of attack we’ve looked at in this article, there are also some non-technical types of social engineering — like tailgating, where someone follows a person into a space that’s off-limits to them. This is also often practiced in connection with media dropping, where data storage devices infected with malware, such as USB sticks, are left lying around in plain sight. To collect information, criminals can also sneak a peek at your laptop, watch you entering your PIN at an ATM (shoulder surfing), or fish confidential documents out of the trash can (dumpster diving).
However, we’ll focus in the following on the technical side of things as well as popular social engineering strategies.
1. Phishing
Phishing involves sending scam emails en mass that come from a seemingly legitimate sender and appear deceptively real. Compared to spam emails, which are usually just super annoying, cybercriminals use phishing emails to try to get their hands on our sensitive data such as login details and account information or to smuggle malware onto our computers via email attachments.
To take their deception to deeper depths, they sometimes also use email spoofing and manipulate the email header to display a different address — one that we trust — to the one the email actually comes from. You can easily reveal if the sender is who they claim to be by hovering over the email address with your mouse pointer (Windows) or clicking the small arrow next to it (Mac) to reveal the actual cryptic-looking sender address.
Phishing emails from banks and online payment services such as PayPal are particularly widespread. Among their tactics, they might ask you to change your password or confirm your login details. This is often presented as a security measure, suggesting you do something right there and then to pressure you into acting rashly. Check out our blog on PayPal scams for more details.
These emails, which are getting better all the time in terms of language and design, usually try to entice users into clicking the included link that leads to a phishing page. If you were to do as you’re told and enter your login details on this fake web page, the scammer can then access that online account. They can now order things in your name and/or change the password and essentially lock you out.
Top tips to protect yourself against social engineering method No. 1
It’s a great idea to use a password manager and browser protection extension to protect yourself against phishing attacks. The great news is that both are included in solutions like Avira Free Security — plus you get free antivirus protection on top. Whereas Avira Browser Safety helps you block phishing web pages and other malicious web content, Avira Password Manager helps you protect your online accounts on your different devices.
The corresponding Android and iOS apps include a feature to generate two-factor authentication (2FA) codes. This can make it much more difficult for cybercriminals to access your online accounts — even if they have your password and other login information. A password manager also helps you create and store super-strong passwords for your various online accounts.
Our advanced all-in-one solution Avira Prime for Windows even includes email protection to help defend yourself from both phishing links and malicious attachments.
Phishing subtypes and variants:
- Voice phishing (vishing): Although at its heart still a form of telephone scam, the increase in technological options means vishing attacks are now also carried out via voice messages, VoIP (voice over IP) calls, and can even be automated.
- SMS phishing (smishing): Smishing involves phishing by text message. Hallmarks include being asked to verify an online account or something similar.
- Spear phishing: Scammers specifically target employees of a company to obtain trade secrets or confidential data and information. If high-ranking executives are the target, this is also referred to as whaling.
- CEO or boss scam: In contrast to the above, here the scammer poses as a high-ranking executive and approaches “their” employees for information or money. Examples can include a company’s accountant being instructed to transfer money abroad without mentioning it to anyone else.
- Angler phishing: In this type of phishing attack, scammers create fake customer support accounts of well-known companies on social media platforms to lure dissatisfied customers. If someone complains on this platform, the scammers contact the customer and pretend to be a service employee or IT expert who wants to fix the issue. They then trick the user into providing information or getting them to click a malicious link.
- Search engine phishing: Cybercriminals use search engine optimization (SEO) to rank their phishing web page at the top of the search results to attract as many visitors as possible to their malicious web page.
2. Pretexting
This is an area where scammers really get creative, sometimes inventing very elaborate stories to gain their victims’ trust and convince them to share sensitive data or transfer money. This social engineering strategy is often used in spear phishing attacks against company employees and also in the grandparent scam.
The scammers usually pose as a line manager, service providers, tax advisor, or similar to the employee and describe a credible situation that gives the victim a good reason to do what the scammers want. The strategy works particularly well if the cybercriminals have prepped well enough and gathered loads of background knowledge about the person and the company in question.
3. Baiting
Baiting involves using some form of physical or digital bait like a free app to download, a free product, some money, or another tempting deal or offer. The best known example of this type of social engineering is probably the now notorious Nigerian prince.
The victim is promised a portion of the prince’s enormous fortune, which they’ll only receive once they’ve made the upfront payment. The reasons why the payment is required to access the assets are as varied as the different flavors of the Nigeria connection scam, which mostly involves advance fee fraud.
4. Honeytrap & sextortion
With this type of social engineering attack, love-hungry people are lured into honey traps, which is why they’re also called love or romance scams. To ensnare their victims, the love scammers create fake profiles on dating portals and pretend to be a young and attractive person looking to marry, often from Eastern Europe.
Once someone has taken the bait, they build an online relationship with the victim and gradually build trust. The scammer then claims to be in financial distress and in need of help, such as for medical treatment, or asks for travel money so they can meet in person. And you guessed it: After receiving the money, they break off all contact — or only ask for further help.
Other cases may result in sextortion where a scammer also contacts their victim via a dating platform or a social network and pretends to be someone attractive. After the getting-to-know-you phase, the perpetrator lures the victim into a sexually compromising situation, records it (or at least claims to have done so) and blackmails the victim by threatening to publish the footage.
5. Watering hole
This social engineering strategy involves luring certain people or groups of people to a watering hole of their choice, meaning a website popular in their circles that cybercriminals have infected with malware.
6. Quid pro quo
Quid pro quo, which is Latin for “a favor for a favor”, is an economic principle that requires someone who gives something to receive something in return. An example of this type of social engineering method is surveys conducted by supposedly reputable companies that promise participants a high-value gift in exchange for their — naturally sensitive — data.
7. Scareware
Scareware is also a social engineering method. It can come in the form of a pop-up that appears to be an operating system notification or one from the user’s antivirus software reporting an issue. It might also come in the form of an email that uses empty threats to either blackmail the person out of money or inject malware. In both cases, the user is frightened and urgently “advised” to act fast — unfortunately to their disadvantage.
Why is social engineering so dangerous?
A successful social engineering attack can cause immense damage and harm, and not only to companies but also to private individuals — affecting them on several levels. In addition to the harm on an emotional level, such as loss of trust, shame, and disappointment, it can also result in financial damage — either directly through payments to the scammers or indirectly through data or even identity theft.
That’s because if your sensitive personal data or access details to your online accounts fall into the hands of cybercriminals, they can misuse this data for their own purposes. For example, they can shop online in your name, take out loans, open accounts, take out subscriptions, or offer your data for sale on the dark web.
The good news is that if you’re the unfortunate victim of identity theft, help is at hand thanks to Avira Identity Assistant to restore your identity1. In addition, Dark Web Monitoring2 scans the dark web for personal data and information you provide, such as your email addresses and bank account and credit card numbers.
How can you protect yourself from social engineering?
Your best protection against social engineering attacks is to spot them. So if in doubt: Even though your instinct is to trust, be suspicious and check if everything adds up first — especially when there seems to be an urgent need to do something or danger is imminent. That said, even though social engineering attacks target human vulnerabilities, there are some precautions you can take as well as technical solutions you can use to protect yourself.
Tips to protect yourself against social engineering attacks:
- Check emails asking for sensitive or personal information, or which seem suspicious, for phishing characteristics.
- Never share your passwords, logins, or account information via email, text message, or over the phone.
- Be cautious and check web pages to ensure they’re legit as well as any links in text messages, emails, or social media.
- Be wary of contact requests from strangers on social media such as Facebook, Instagram, or TikTok. Be equally vigilant when interacting with others, especially with profiles of strangers or unknown users.
- Be careful about what information you reveal to whom in your private and professional networks.
- Use two-factor authentication (2FA) to strengthen the protection of your online accounts and use unique and strong passwords. That’s important since if cybercriminals get hold of the login details for one of your online accounts, your other accounts won’t necessarily be at risk.
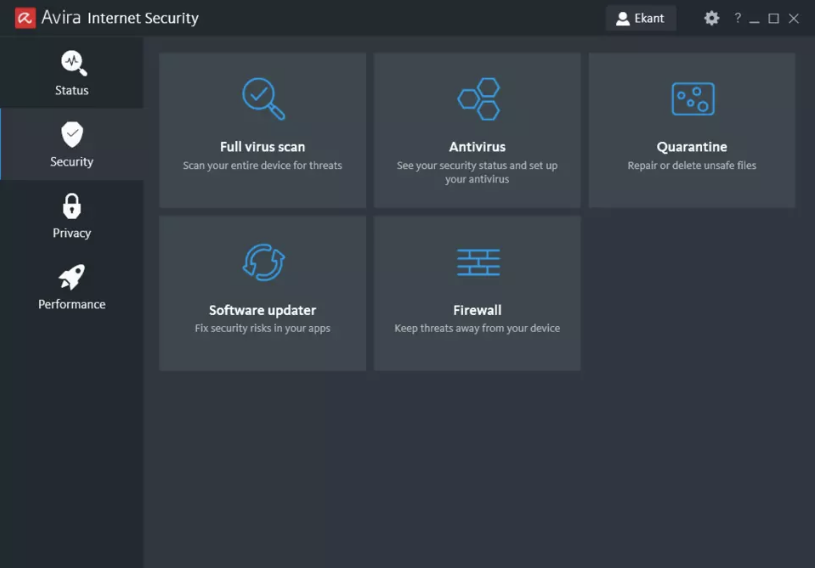
- Use an all-in-one protection solution like Avira Free Security with key features like antivirus protection, browser protection, and a password manager with authenticator functionality.
- Protect your mobile devices too, such as with Avira Antivirus Security for Android or Avira Mobile Security for iOS.
1 For identity recovery assistance, contact customer services (Mon-Fri, 9am-4pm). An identity recovery specialist will then call you back within 48 hours.
2Dark Web Monitoring is only available to residents of Germany. The email address you use to purchase the product will then be monitored immediately following activation. Log in to your account to enter more information to monitor.














