Downloaded a few audio books or your music library and then started shooting countless photos on vacation only to find that suddenly your smartphone or tablet’s memory is all used up and there are still loads of things you’d like to photograph?
It’s high time you ought to think about storing data in the cloud. The cloud is a virtual memory where you store your data. You then access it via the internet without using up your (mobile) device’s storage space. Cloud services are super simple to use and convenient — but have you ever thought about the state of cloud security?
Read on to learn how you can store your data more securely in the cloud, how to detect security risks, and, above all, how to avoid them.
What is cloud security?
Cloud security is an essential part of cloud computing (meaning the delivery of computing services, like storage and apps, over the internet) which itself is becoming increasingly popular.
iCloud, Dropbox, and other cloud services are growing in popularity among home users — and many companies also appreciate the obvious advantages. In addition to the possibility of decentralized yet connected processing of information, cloud computing is cheaper, provision is extremely easy, and the data volume is scalable. This conserves your own server capacity and saves storage space — which many also appreciate for private purposes.
If companies or private individuals use a cloud, their data is stored on external providers’ servers — so even if you delete this data on your device or your smartphone breaks or even gets stolen, it’s not lost. That’s another big benefit.
Cloud security refers to a fairly comprehensive set of policies, technologies, applications, and controls, all deployed to help protect our data, applications, services, and associated infrastructure in a cloud.
Cloud computing and cloud security are therefore closely linked, and cloud providers need to consider many measures to secure their services.
For example, the risk of downtime must be minimized, strategies for possible data loss must be implemented, and, of course, defense mechanisms for impending hacker attacks or unauthorized data access must be put into action.
Cloud security takes all relevant processes into account
Best practice in cloud security considers almost all the processes and instances that need to work together properly to ensure the security of our data in a cloud solution.
Cloud security measures include all physical devices or hardware involved, such as the data servers, routers, power supply, climate control, and cabling.
And of course the cloud provider’s operating systems and software solutions must also be designed to function 24/7. After all, very few of us will want to tolerate using a cloud that’s temporarily unavailable due to system updates or faults.
Last but not least, cloud providers must ensure that we, as users of the cloud, have access to our data stored in the cloud via all our digital devices — no matter which hardware or operating systems we use.
Security risks in the cloud
There are various security risks in the cloud that providers are more or less responsible for. In many cases, providers offer what are known as API interfaces that make it easier for companies to connect other components to the cloud. And the more interfaces that are integrated, the greater the risk that cybercriminals can gain access to the data stored in the cloud through vulnerabilities in the configuration of those interfaces.
Such interfaces are probably less relevant for personal use, but you can probably guess that the key step to using the cloud securely is being aware of the greatest security risks that can arise when using a cloud solution.
Data loss security risk
Cloud services are basically exposed to the same threats as corporate or home networks and computers. However, the sheer volume of data makes them a far more attractive target for hackers.
Cloud providers do a good job of protecting their services — and in doing so your data — but ultimately we users or the IT managers in the companies themselves are responsible for the security of our cloud data.
Data theft as a security risk in cloud solutions
Completing a two-factor authentication step — something that’s now required by law — to log in to your online bank account is something you’re probably familiar with.
Cloud services now also offer multi-level authentication, such as one-time passwords or authentication by telephone or using smart cards. This way, cybercriminals have less of a chance of logging in to your cloud accounts with stolen passwords. However, you also need to turn on these advanced authentication options because they are not yet mandatory for cloud services.
Top tip: An advanced password manager gives you the power to protect your devices — including your cloud service. Avira Password Manager can help you minimize the security risk in the cloud, generating strong passwords for all your accounts and offering a smartphone authenticator that can add a further layer of security to your accounts.

Permanent data deletion by hackers as a security risk
Cybercriminals are known to try to harm businesses by permanently deleting cloud data. Such attacks can also affect home users, which is why you should also schedule regular backups of your cloud content.
How does cloud security work?
As mentioned, cloud solutions include a wide range of measures designed to enhance cloud security. Many of these measures focus on the IT infrastructure, which we, as users of such a cloud, are completely unaware of. Read on as we delve into two key aspects.
Identity and access management creates cloud security
An integral part of cloud security is identity and access management (IAM), which is critical for security and regulatory compliance.
The term identity and access management covers all the processes used in companies such as to grant or deny employees authorization to view, edit, and save data in a cloud service.
Behind this is usually a very sophisticated system of roles and rights, because in larger organizations it must be ensured that each individual has the appropriate access rights for them to be able to complete individual tasks.
Administrative functions in cloud solutions
In addition and closely linked to identity and access management, various other administrative functions are defined and monitored as part of cloud security.
It’s not just about managing such things as user lifecycles, application access, or individual log ins. Ultimately, administration also includes ensuring that sufficient server capacity is available at all times. For this, all instances and components that communicate with each other in the background and which are invisible to us must function properly.
How can you help make the cloud a secure place?
As mentioned, advanced password protection is essential because it helps to strengthen the security of your data in the cloud. In this regard, it’s best to use a password manager that offers multi-level authentication.
You should definitely also encrypt sensitive data, such as PDF contract documents, if you store them in the cloud at all.
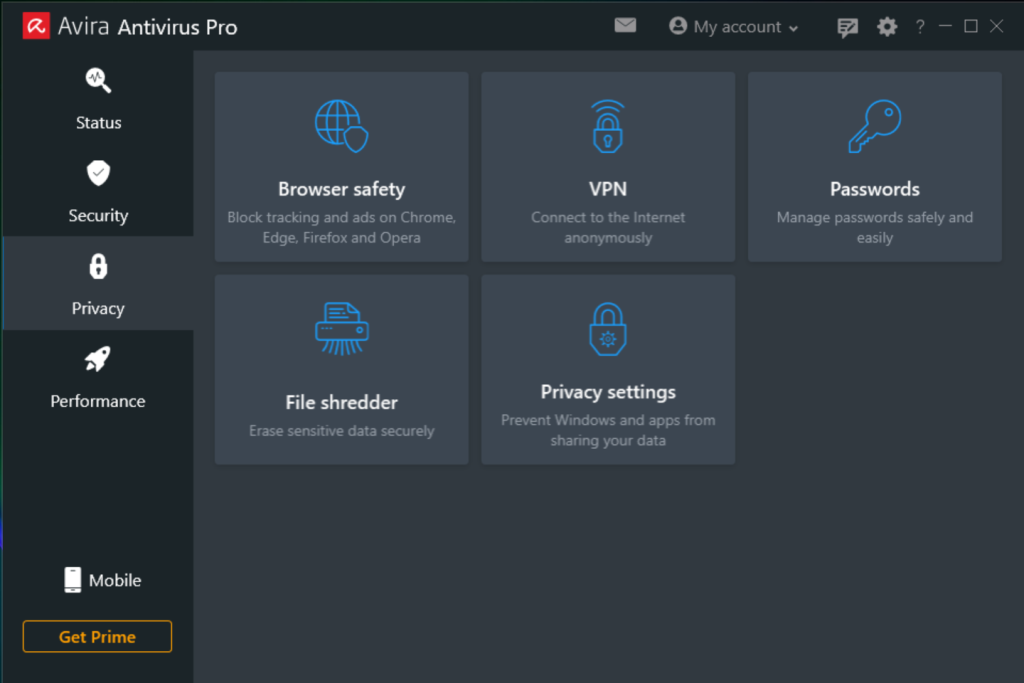
Antivirus programs with tools that help improve security by using the cloud
With an antivirus program, you have the option of using the cloud to detect malicious files more quickly.
Avira Protection Cloud enables you to benefit from neuralgic technologies, which are a sort of early warning system that can help detect critical file characteristics faster and protect possible gateways. This is all thanks to the ability of these cloud-based technologies to check the stored files in near real time. As a result, Avira Protection Cloud offers a better chance of being able to detect a possible virus attack in the cloud.
Because attacks are mapped in the cloud in addition to being checked in real time, this speeds up the detection of new cyberattack patterns — making it even more difficult for hackers to analyze and evade built-in defenses.
And best of all: Even the freeware version of Avira Antivirus includes Avira Protection Cloud, so you have both an antivirus program AND a faster detection rate for malicious files in the cloud.
A must-have when accessing the cloud using public Wi-Fi hotspots: A VPN
Storing data in the cloud is incredibly convenient because you can access your content from anywhere in the world via the internet. However, public networks aren’t exactly secure, which is why it’s a good idea to use a VPN (virtual private network) whenever you want to access content on your cloud service. You can even go for a VPN specifically for your operating system like the VPN for Android.
Avira Phantom VPN can help you protect your online activities as well as access to your cloud service.

Top tip: Avira Phantom VPN is an integral part of Avira Antivirus Pro and Avira Prime — tools that not only strengthen your online privacy but also help you encrypt the data you send and receive over your internet connection.