No longer restricted to state organizations buying access to NSO spyware , monitoring and surveillance software, known as Stalkerware, has been developing steadily. Thanks to fast growth in mobile device penetration, aggressive app developers, and a lack of legislative protection, Stalkerware is now available to just about anyone with a smartphone, making it easy to spy on spouses, family members, or friends.
Recognizing that monitoring software is a rapidly growing threat category, Avira has proudly joined the Coalition against Stalkerware. Comprising several IT security companies and organizations, the coalition will work together, sharing information and developing a common approach to stopping privacy violations, in order to protect against domestic violence.
Spotting Stalkerware is not so easy
Stalkerware apps may compromise a user’s privacy and the security of the local system. But identifying Stalkerware apps is not a simple and obvious task. One reason is that these might be a dual-use app, meaning the same app could be legitimately installed and used by a person to monitor their own device, or it could be secretly installed on another person’s device without their knowledge or consent and used to spy on their activities. The list of Stalkerware apps can include malicious programs, commercial spyware built specifically for this purpose, or legitimate apps used maliciously. An example of the latter is abusing the use of monitoring apps meant for parents to track children to track an intimate partner instead.
These apps have a long list of technical capabilities, too. Some may include call recording, device tracking, remotely taking pictures/videos, remotely monitoring and uploading data from the device, and more. Then there are operational functions such as the ability to work in stealth mode (where the user is not notified about the monitoring), disguising itself as a system process or utility program, and preventing the uninstallation or disabling of antivirus software.
Avira is tackling Stalkerware with others
The combination of technical capabilities with specific operational functions makes spying on intimate partners easier and more accessible — and facilitates abuse by people with bad intentions. Avira has developed its own list of around 20 points for identifying Stalkerware and we are not the only organization working to consistently identify this threat. The Coalition Against Stalkerware is exceptionally important in helping the industry reach a consensus over the criteria for evaluating what is, can, and should be considered Stalkerware and then creating a proper detection for it.
Is the number of Stalkerware apps decreasing?
From our 2019 research, popular Stalkerware apps that were available included: FlexiSpy, mSpy, Cerberus, Trackview, HelloSpy, ATTI Shadow Tracker, Retina-X, iKeyMonitor, and FoneMonitor. By last July Google had agreed to remove some of them, with Z6Mag reporting on this development.
This year, Google is taking a further step in the right direction. The company recently announced that effective August 11, 2020, it will ban ads for Stalkerware. This is an important move as although many Stalkerware apps are already banned from Apple and Google’s official app stores, companies are currently able to promote these kinds of apps available on third–party sources.
Avira still sees Stalkerware on the market
However, despite these efforts, we still see Google Play hosting Stalkerware apps. Here is an example of an app that Avira has uncovered and some of the reasons why we consider it to be Stalkerware.
All Tracker Family available on Google Play as of November 2019. According to the app store description, its features include:
- Access to location, phone calls, camera, microphone
- Monitor notifications sent in the status bar from any app such as Messenger, WhatsApp, and Viber
- Screen mirroring in real time – stream the screen of a device to any browser
- Monitor location by GPS tracking, phone calls, camera, and microphone from other devices
- Live video tracking from device camera
- Monitor surroundings with live audio tracking from the device microphone
The app is cleverly advertised as a convenient means to allow you to give your parents or partner total or partial access to your device.
After installing it on a “victim” device and connected it to an account, we can see details about the device on alltracker.org – the app’s web page for showing tracked devices:
The developer (RUSSCITY) has taken care to inform us that any function will send a notification to the device:
“ATTENTION: You CANNOT hide this app! Phone owner will be always notified about each request send to his/her phone. You CANNOT use this software like a spyware or hidden tracking!”
However, even though the application itself has no option to disable notifications, we used the standard Android settings to disable the notifications for this app. This enables a person to surreptitiously install and hide the app on a targeted phone:


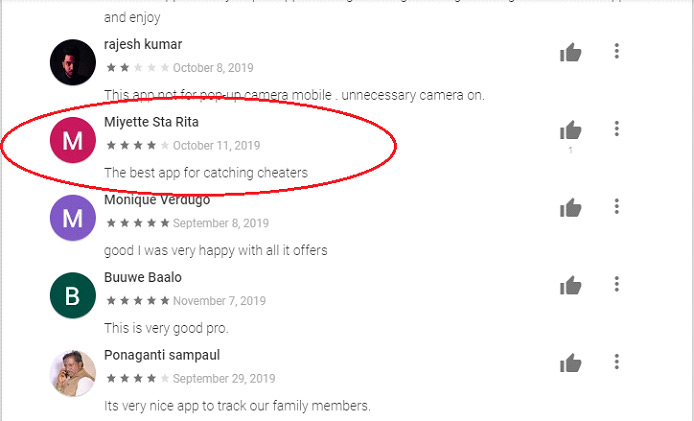
This is an example of an app which can be abused to spy on a significant other remotely. And, as we can see from the Google Play comments, people are actually using it for that exact purpose. For these reasons we consider this a Stalkerware app and are detecting it as PUA/Stalk.Catwatch.spy.