The American National Security Agency is moving one of its in-house tools out into the open-source arena – making its Ghidra reverse engineering tool easily accessible and customized.
That’s quite a switch for a government agency most known for the release of its EternalBlue zero-day exploits. These were subsequently misused to launch the WannaCry and Petya attacks.
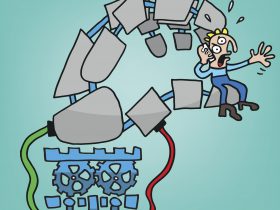
LEGO deconstruction
As mentioned in WikiLeaks’ March 2017 “Vault 7” release, Ghidra is a reverse-engineering platform used to take a completed software apart into its basic parts and elements. If you think of software as a LEGO model, Ghidra helps take this model apart to see the components and layers in its construction, decode how the various parts work together, and maybe help a person make the assembly directions in reverse.
Unlike the previously leaked tools, Ghidra is considered a defensive tool. It is used to take software apart and not hack it from behind. However, as a free and easily accessible tool — download it here — it is certain that it will be used by all sorts of developers and hackers – both the black and the white-hat variety – to help them in their tasks.
Avira takes Ghidra for a test drive
Avira analyst Shahab Hamzeloofard has already taken Ghidra for a test spin around the block and found it an “interesting” platform. “Some of Ghidra’s most interesting features are its code browser, the decompiler that works for all supported processors, and the collaboration capabilities,” said Hamzeloofard. “I think the only comparable reverse engineering tool is IDA.”
The professional competition already comes loaded. “In comparison with IDA, Ghidra doesn’t have a debugger and IDA supports more modules and file loaders,” he added. “There’s already a big community of reverse engineers using IDA, there are different plugins and support, and it’s not so easy to switch to Ghidra.”
Open source, open door?
As a new open-source project, Ghidra will have a dramatic shift from being a well-protected, complete platform for NSA analysts. It will be open for any software developer to use, modify, and even contribute code to help improve the product. Other well-known open-source projects include the Apache HTTP Server, GNU/Linux operating system, LibreOffice, the Mozilla Firefox and Chromium browsers, and the Windows’ Calculator.
There is a robust debate in the security sector over whether or not Ghidra has a backdoor that could allow the NSA to see what users are doing with it — or just a simple programming bug. As an open-source project, with code that is easily accessible, hiding a backdoor would be an operational and a reputational risk. “I think there’s an exaggeration about the backdoor. I don’t think this is really a backdoor it more looks like a little bug,” he added.
NSA makes a public service announcement
The transformation of Ghidra into an open-source project is a huge change. Philosophically, it means that the NSA is feeling secure enough to let anyone use its prize tool. It is also a smooth PR move for NSA, showing that it does more than stockpile zero-day exploits and hack phone conversations. Instead, it is helping make the connected world a bit safer. Besides, it means new hires at NSA might come to the agency already proficient in their reverse-engineering tool.
Operationally, it also lowers the cost bar for taking software apart. In addition to Ghidra, there are a couple tools available in the private sector but these tend to be pricey. As stated in Axios, this step helps “democratize” security research by making tools more readily available.
About that funky name and logo
Ghidra is a character in the Final Fantasy video games — it’s apparently a mistranslated Japanese word for Greek mythological Hydra.
The NSA logo for Ghidra is a dragon-headed snake twisted into an infinity symbol. The tail turns into binary code before being eaten by the dragon. Yes, that code has meaning. It spells out programmers’ traditional first words: “Hello world.”