When you share confidential information face-to-face with others, you’re probably careful not to let others hear — perhaps even whispering so nobody can eavesdrop on your conversation.
Taking precautions also applies to the virtual world, especially as we’re learning every day about the increasing threats of cyberattacks that can affect each and every one of us. What we’re talking about here are things like man-in-the-middle attacks, where hackers manage to sneak into a confidential exchange between two parties.
Read on to learn all about what a man-in-the-middle (MITM) attack is, how to spot one, and how to avoid the possible fallouts.
What are man-in-the-middle attacks?
Using a now very common man-in-the-middle attack, cybercriminals try to read, intercept, or even manipulate the data traffic between two target people.
Once they intercept confidential or personal information, scammers can easily pass themselves off as the person who’s been affected by a man-in-the-middle attack.
As a private individual, this explanation might perhaps mislead you into thinking that man-in-the-middle attacks tend to be less threatening because you’re very careful about sharing your information. However, there are several common types of attack that happen frequently which cast a different light on such a threat, to the extent that make you realize these attacks still pose a danger.
Different types of man-in-the-middle attack
ARP (or address resolution protocol spoofing) is a common type of man-in-the-middle attack.
When you visit a website, for example, the associated IP (internet protocol) address is mapped to a media access control (MAC) address before the page is even displayed. It’s not particularly difficult for savvy cybercriminals to connect this address resolution protocol to a legitimate IP address via their own fraudulent MAC address. This way, they can steal or modify data that was actually intended for the owner of the legitimate IP address.
By contrast, when using a DNS spoofing attack, the attackers manipulate the domain name service (DNS). To do this, they falsify the IP address belonging to a domain or website and when we visit a website manipulated in this way, we end up on the cybercriminals’ servers — all without noticing anything because the “correct” address appears in the browser.
Another type of man-in-the-middle attack is referred to in the IT world as a rogue access point.
Whether it’s your PC, laptop, smartphone, or tablet: All our devices try automatically to connect to the access point of the strongest Wi-Fi network in the vicinity. Cybercriminals set up their own Wi-Fi access point for this type of man-in-the-middle attack. This means that if you’re close to this, naturally unsecured, Wi-Fi network, your device could connect to it automatically. This then gives the attacker free access to everything you send and receive, enabling them to manipulate the traffic however they want.
Man-in-the-middle (MITM) attack methods
Cybercriminals use many different variations of the kidnapping or hijacking method. Before we dive into some of these methods in more detail, here are just a few examples:
- In the case of browser hijacking, for example, malware you’ve ended up installing without you even realizing manipulates your browser settings. This malicious software runs in the background and can wreak havoc, including changing your home page or forwarding your search queries to malicious websites.
- With domain hijacking, hackers — illegally, of course — hijack the domain from the rightful owner and assume the owner’s identity, which is a rather aggressive form of hijacking.
- Content hijacking is when other website content is loaded on top of the actual website’s content.
Session hijacking
In the case of session hijacking, cybercriminals hijack a valid session: When you register and log in to web apps, a session ID records your visit. This allows the website operator to ensure it’s the same user throughout the session, regardless of which areas of the website are visited.
However, because many apps use cookies to send the session ID to the server, it’s easy for cybercriminals to take control of these sessions. Once they hack this session ID, they can use or abuse the app on behalf of the actual owner.
Email hijacking
Email hijacking is another form of man-in-the-middle attack where hackers compromise their target’s email account and gain access. They then monitor communications between your email client and provider unnoticed, using the information for malicious purposes.
In doing so, once they’ve hijacked your email account, when the time’s right attackers can email your bank using your own email address, instructing the bank to transfer money to their bank account. They could also use your email address to take over other online accounts linked to the email address.
Sniffing
In a sniffing attack, hackers illegally “sniff out” sensitive data such as online banking or log-in details. Sniffing was originally used to analyze networks, and system admins can also use this method to identify errors in corporate networks.
By contrast, cybercriminals misuse the tools available for this purpose to obtain data that isn’t encrypted strongly enough. Once they’ve sniffed out this data, they decode it and can then use it for their own nefarious purposes — such as to work out passwords, read emails, or find out which users communicate with each other via which protocols.
Packet injection
Packet injection is based on sniffing, meaning hackers first sniff out security holes to then inject malicious data packets into actually valid data communications. After injection, the bad packets blend with the valid ones in the communication stream.
Spotting a man-in-the-middle attack
MITM attacks are not always easy to spot, but their presence creates disturbances in otherwise regular network activity that you, the user, can also notice.
Being unexpectedly and/or repeatedly disconnected can be an indication that you have fallen victim to a man-in-the-middle attack. That’s because cybercriminals deliberately disconnect you from the network to intercept your usernames and passwords — as soon as you try to reconnect, they get in the middle, so to speak.
When surfing, be sure to keep an eye on your browser’s address line: Strange addresses in the browser address bar can be another red flag. If, for example, https://go00gle.com appears there instead of the correct address https://www.google.com, you need to check out what’s going on.
Also, be extra careful when using public Wi-Fi hotspots. It’s precisely because of their very nature that security restrictions are usually less restrictive than on a private or company network — making it really easy for cybercriminals to get in the middle. To trick us into connecting, attackers like to create fake networks with familiar-sounding names like WiFi_Bus (instead of the actual name BusWiFi). If you connect to the attacker’s Wi-Fi hotspot, attackers can easily see anything you send over that public Wi-Fi network.
Avoiding man-in-the-middle attacks
There are a number of steps you can take to proactively avoid and protect yourself from a man-in-the-middle attack.
Let’s start with your router, which many of us don’t consider to be a particularly critical component at all. However, it really makes a difference whether you use simple log-in details or a network name that’s not easy to assign to you in combination with a strong password.
When surfing, make sure you only access websites that use the HTTPS security protocol, meaning those that have an HTTPS address. Most browsers show a security warning as soon as you visit a website with an outdated security certificate and let you decide whether you want to view the site anyway. Your best bet is to run for the hills.
An increasing number of website operators are now using two-factor authentication (2FA) when you log in. What is mandatory for banks also makes sense for many other portals and websites — which is why many operators are increasingly offering them. So don’t be afraid to use 2FA for your accounts.
A VPN can protect you from man-in-the-middle attacks on public Wi-Fi networks
If you frequently surf using public networks, a VPN — a virtual and private network — is essential to strengthen your protection against man-in-the-middle attacks and many other cyberthreats. When connecting via such a VPN network, your actual IP address is hidden. Instead, search engines and website operators see the VPN’s IP address — and cybercriminals also have a lower chance of using a man-in-the- middle attack to get your data.
Avira Phantom VPN, for instance, can help you improve your protection when using public Wi-Fi hotspots. Not only can you get your VPN for free, but you can also choose your preference for the operating system you’re using. For example, if you are using Windows, you have the option to download the VPN for Windows.

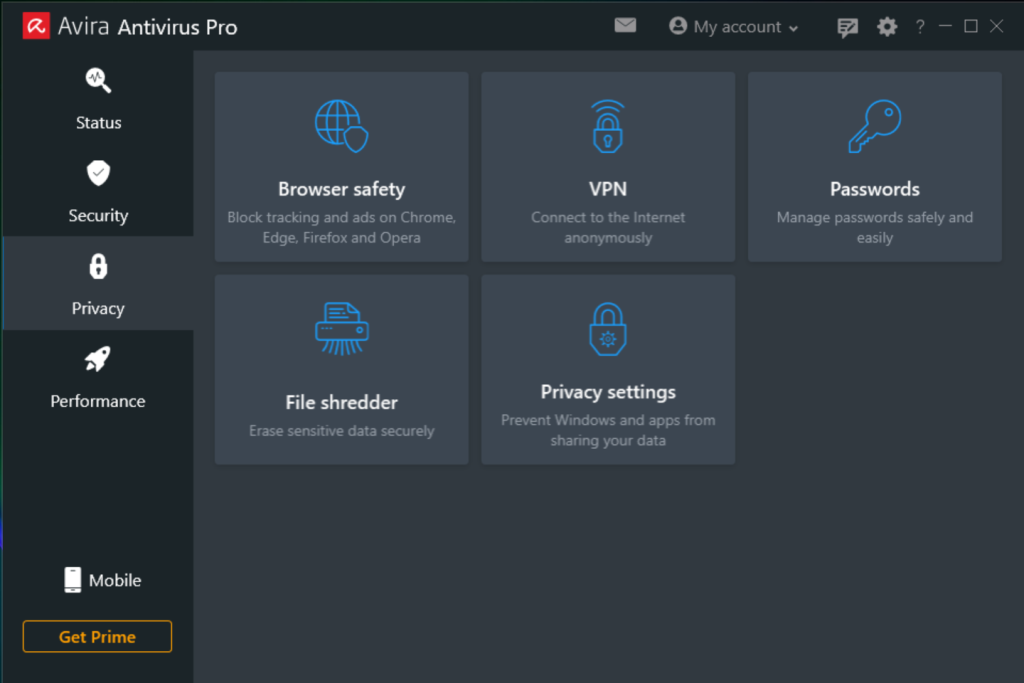
Avira Phantom VPN is an integral part of Avira Antivirus Pro and Avira Prime — programs that can strengthen not only your online privacy but also improve your device’s performance and especially security on public Wi-Fi hotspots.
Install an antivirus program or app on your device
We cannot stress it enough: Every device should have an advanced and proven antivirus program installed on it — especially as it can indirectly strengthen your protection against man-in-the-middle attacks. That’s because the latest antivirus programs are designed to protect your devices from a wide range of cyberthreats as they take into account the latest malware developments.
You can also increase your malware and virus protection with Avira Free Antivirus, so cyberfraudsters have a lower chance of carrying out a successful man-in-the-middle attack. This won’t stop them from launching such attacks, but it’ll help you avoid them.
Avira Free Antivirus is a lightweight antivirus program that won’t sap your system’s resources. With this solution, you can defend yourself from malware — and when it’s scanning for threats, it also considers device performance and your online privacy.















