You could think that malicious Office macros are a thing of the past. They are not a major threat anymore, but they still represent a potential risk for unsuspecting users.
Since Microsoft Office enabled documents to embed macros that can even do complex actions such as dropping malicious executables, malicious office macros were used in the malware landscape.
When Office XP was released in 2001, it disabled macros by default: as a consequence, malicious macros were not so efficient to infect users, so their use in the malware landscape rapidly declined afterwards.
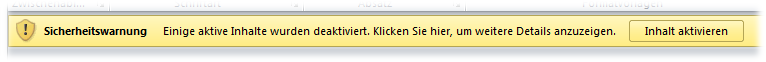 However, it doesn’t mean that the threat is not present anymore, especially in corporate environments where users may leave them activated by default.
However, it doesn’t mean that the threat is not present anymore, especially in corporate environments where users may leave them activated by default.
And the document can try social engineering to convince you to re-enable them.

The file also contains something weird:
 If you scroll down, you notice something unusual:
If you scroll down, you notice something unusual:
that invisible but underlined text is actually a malware file (4D 5A is the signature of a Portable Executable file), encoded in the document, but in white font on white background.
 This is what it looks like if the text is back in normal color.
This is what it looks like if the text is back in normal color.
On execution, the macros remove this hidden text, to remove traces of maliciousness.
So, be careful: don’t enable macros by default, and don’t enable them for unusual documents.
Analyzing malicious office macros out of a document
Until Office 2007, Microsoft used the OLE Compound File Binary Format. Here is an accurate summary of the format:
 because it’s actually a complete filesystem, with multiple FAT formats, sectors, streams, defragmentation…
because it’s actually a complete filesystem, with multiple FAT formats, sectors, streams, defragmentation…
So for your sanity, we’ll avoid the details here as much as we can…
Starting with Office 2007, the default format was the “XMLs in a ZIP” Office Open XML.
But to store macros, even Office Open XML still uses the OLE format: they are located in the vbaProject.bin file inside the ZIP archive.
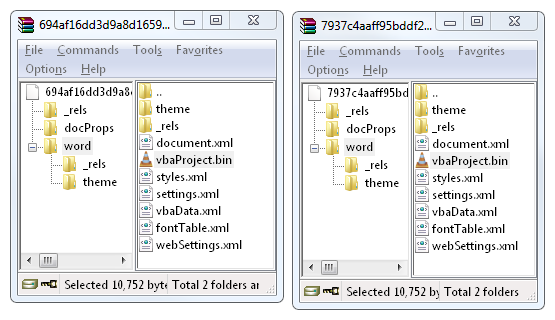 So in any case, we need to deal with the OLE format to extract macros: either the whole document (< Office 2007), either the vbaProject.bin file (later versions),
So in any case, we need to deal with the OLE format to extract macros: either the whole document (< Office 2007), either the vbaProject.bin file (later versions),
Just for your information, this is what such a OLE file looks like from a high level perspective.
 (don’t show that to your kids, they might look away from computers for ever)
(don’t show that to your kids, they might look away from computers for ever)
If you still want to know more about the OLE format, you may want to watch Bruce Dang’s presentation on the topic.
So first, extract the vbaProject.bin file from the ZIP. Then, ask OfficeParser to extract the macros: luckily, it does all the magic for us.
 it displays an error, but the file NewMacros is still correctly extracted.
it displays an error, but the file NewMacros is still correctly extracted.
And then, you can clearly tell immediately the intent of the file… it’s pretty obvious (and actually, quite disappointing)…
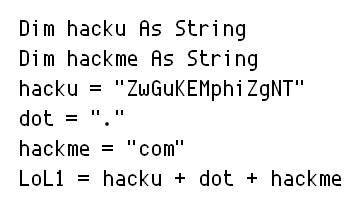 Obvious variable names
Obvious variable names
 They are so proud of it that they re-used it multiple times…
They are so proud of it that they re-used it multiple times…
Ok, let’s stop here. You already get the idea about the intents of this file, and now you know a simple method to analyze malicious Office macros yourself.
Sadly, not much to learn from this threat: excepted that it’s a good thing to practice on a ‘forgotten’ file type, that could still be used today to infect users.
Related tools:
- OfficeMalScanner: doesn’t parse OLE file, but tries to extract embedded shellcodes and binaries.
- OleFileIO_PL: a more advanced parsing library than OfficeParser, but with no direct macros extraction ability.















