Locky ransomware has shifted into an encrypted lockdown mode and is now protecting the network communication between victims and the command & control servers with public key encryption.
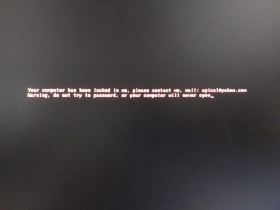
Locky ransomware burst onto the scene in February and has made headlines by encrypting files and shutting down the operations of hospitals and large organizations. The ransomware is primarily distributed via emails and relies on social engineering for its downloader to be opened or activated. Depending on the company size, the ransom can vary from around 200 to 15,000 Euro. It is virtually impossible to decrypt the files without the key from the Locky developers.
The changeover gives Locky workings greater secrecy and gives the overlords distributing the ransomware tighter control over their network infrastructure and restricts researchers’ ability to eavesdrop on botnet activities.
“The addition of the public key encryption of the network communication throws a wrench in the ability of outsiders to track or even influence Locky activities,” said Moritz Kroll, malware researcher at Avira. “You now have to have the RSA private key – the other half of this equation – to tap into the network. And the Locky developers are clearly keeping this to themselves.”
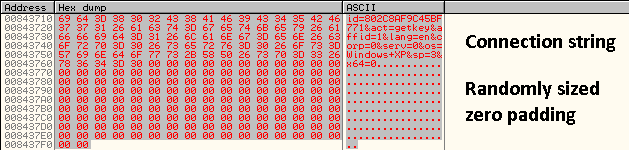
Locky has always sent a specific public key to each victim as part of the file encryption process. Now it’s also using an RSA public key, which is provided with the sample, to encrypt the keys for C&C communication. The new development has Locky sending out one binary blob with an AES-CTR encrypted connection string as well as one RSA encrypted block with two keys and a HMAC-SHA1 hash.
“The private RSA key is needed to extract the request and response keys which then sets off one more decryption of the request message and one hash verification. If you don’t have this RSA key, it is neither possible to understand the request nor to create a response that the Locky Trojan can decrypt and understand,” explained Kroll.
The change restricts the information that security researchers can find while eavesdropping on Locky activities. Previously researchers have been able to sinkhole the domains of Locky’s DGA (domain-name generation algorithm) and provide statistics on infections and activities:
The changes mean that a sinkhole can still get IP addresses of victims and geo-locate them, but no longer collect information on infected operating systems, the potential size of the victim, and the ransom demanded (without VAT).
Given the lack of a code of honor among thieves, the encryption may be a preemptive step to ensure that the originators remain in control of their enterprise and the Locky brand. Other cybercriminals have already tried to make knock-off versions such as AutoLocky.
“It makes you wonder if some other malicious actor was able to sinkhole the Locky C&Cs to distribute their own public keys for encryption with their own ransom text – and this is a way to stop it,” said Kroll. “The Locky originators could be getting upset: ‘We are doing the real work and someone else is stealing our hard-earned money’.”